Exploring The Impact Of Malvertising On Government, ISPs & The Fortune 100
Most of the malvertising disclosures we have done to date have centered around attacker infrastructure, exploits, and IOCs. In this blog post we will explore the threat of malvertising from the other end of the tunnel and look at what organizations are being disproportionately targeted in these attacks as well as which threats they are the most likely to face. Our focus will be on Fortune 100 corporations as well as government institutions, and ISPs.
Methodology
Confiant protects publishers and their audiences from malvertising attacks via client-side integrations that block malicious advertisements in real-time. We have coverage on tens of thousands of websites and have monitored over 1 trillion digital advertising events since we have introduced our blocking product.
For every malvertising incident that we block, we collect some metadata about where that ad was served. We don’t store any PII, but for any given incident we know things like device, browser, and geo to name a few. When we aggregate these incidents by ASN, we can explore which networks emerge as outliers when it comes to attack volumes.
Note: ASNs are gathered via MaxMind lookups of client IP addresses.
Exposure Index
The observations that we present in this blog post are based on 3 months of client-side monitoring from Oct. 15, 2019 — Jan. 15,2020. The total number of global malvertising incidents for this time span is ~378MM.
A malvertising incident within the context of this blog post is when an ad is shown on one of our publisher customer’s properties, but prevented from rendering by our security solution. Most incidents are recognized by either the presence of a domain or “creative ID” that is deemed to load unsafe resources, but many times it can be a heuristic based determination as well.
In order to normalize the data presented in this blog post, we introduce the concept of an “exposure index”.
Since we are dealing with such a large dataset, it’s untenable to crunch billions of rows of data that account for each individual ad impression or malvertising incident. Instead, we have taken a one day snapshot of our monitoring volumes by ASN (which is stable day over day) and used this as a baseline in order to establish a ratio that denotes how exposed a network is to malvertising attacks.
For example, an exposure index of 1 is average and an exposure index of 1.01 means that an organization is 1 percent more exposed than average. Please keep this in mind when reviewing the data, as raw blocking statistics can be quite misleading otherwise.
Malvertising Threat Actors
We see many malicious campaigns day in and day out. When we analyze the unique characteristics and modus operandi of these attacks, we’re able to attribute a significant amount of activity to several persistent groups. We provide a brief synopsis on some of the more impactful attackers below, as we have chosen to present our findings based on the activity of these outliers.
eGobbler — This Asia-based attack group has a history of exploiting obscure browser bugs to bypass built-in browser protections against pop-ups and forced redirects.
Malvertiser ‘eGobbler’ Exploits Chrome & WebKit Bugs, Infects Over 1 Billion Ads
We have written about the threat actor eGobbler extensively on our blog over the last year as they’ve continued to…blog.confiant.com
Massive eGobbler Malvertising Campaign Leverages Chrome Vulnerability To Target iOS Users
As publishers have become increasingly aware over the last week, there’s a series of rampant malvertising campaigns on…blog.confiant.com
Scamclub — Stands apart from their malvertising peers in their approach toward evasion. Whereas most high-profile malvertisers choose to hide behind carefully crafted fingerprinting and targeting, Scamclub relies on bombardment tactics designed to overwhelm platforms and security vendors by creating a flood of dangerous demand that they hope will spill beyond any anti-malvertising gatekeeping.
Malvertising Attack Hijacks 300 Million Sessions Over 48 Hours
Nov 12th Malvertising Attack Serves Adult Content and Gift Card Scamsblog.confiant.com
Yosec — One of the new kids on the malvertising block. Named after their CTA messaging along the lines of “Your Mac Security”, this attacker based in Eastern Europe has been consistently serving up redirects to threatening malware pages. They are a major source of distribution for the notorious Shlayer trojan:
OSX/Shlayer new Shurprise.. unveiling OSX/Tarmac
Mac Spyware Shlayer is now dropping an entirely new malware we called OSX/Tarmac.blog.confiant.com
SelfRef10 — Specializes in forming bi-directional ad tech relationships that empower them both to buy and to sell so that they can play both sides of the coin. They’ve shown no signs of slowdown in the last half year and continue to run desktop redirect campaigns, often choosing vague domains as delivery vehicles.
Hong Kong Based Malvertiser Brokers Traffic To Fake Antivirus Scams — Over 100 Million Ads…
This blog post explores the techniques and tactics of a persistent malvertiser that operates under a company called…blog.confiant.com
GPack77 — This threat actor based in Latin America is responsible for mobile redirects (Android) that primarily target Europe.
MWC — This attacker is behind some of the ubiquitous giveaway or sweepstakes scams that are often byproducts of forced redirect campaigns.Typically they masquerade as e-commerce brands, going as far as creating an entire digital presence for each of their campaigns by stealing existing brand’s websites and hosting them under typo domains.
Zirconium — Zirconium runs a very sophisticated malvertising operation that’s notable for unique fingerprinting techniques that are carried out in multiple stages. This group, which just two years ago was focused on churning out fake agencies by the handful in order to win seats on buying platforms, has since shifted their approach, but are still running similar tech support focused malvertising campaigns.
Zirconium was one step ahead of Chrome’s redirect blocker with 0-day
On January 15, Confiant exposed the activity of the Zirconium group, spreading malicious ads via a network of fake ad…blog.confiant.com
A note on unattributed incidents:
It’s important to not get overzealous with attributing independent campaigns or incidents to a single attacker as it’s a discipline that blurs boundaries between art and science, and inaccurate assessments can have dire consequences. Attackers that are not categorically relevant to this blog post are reported as “Other” in the dataset.
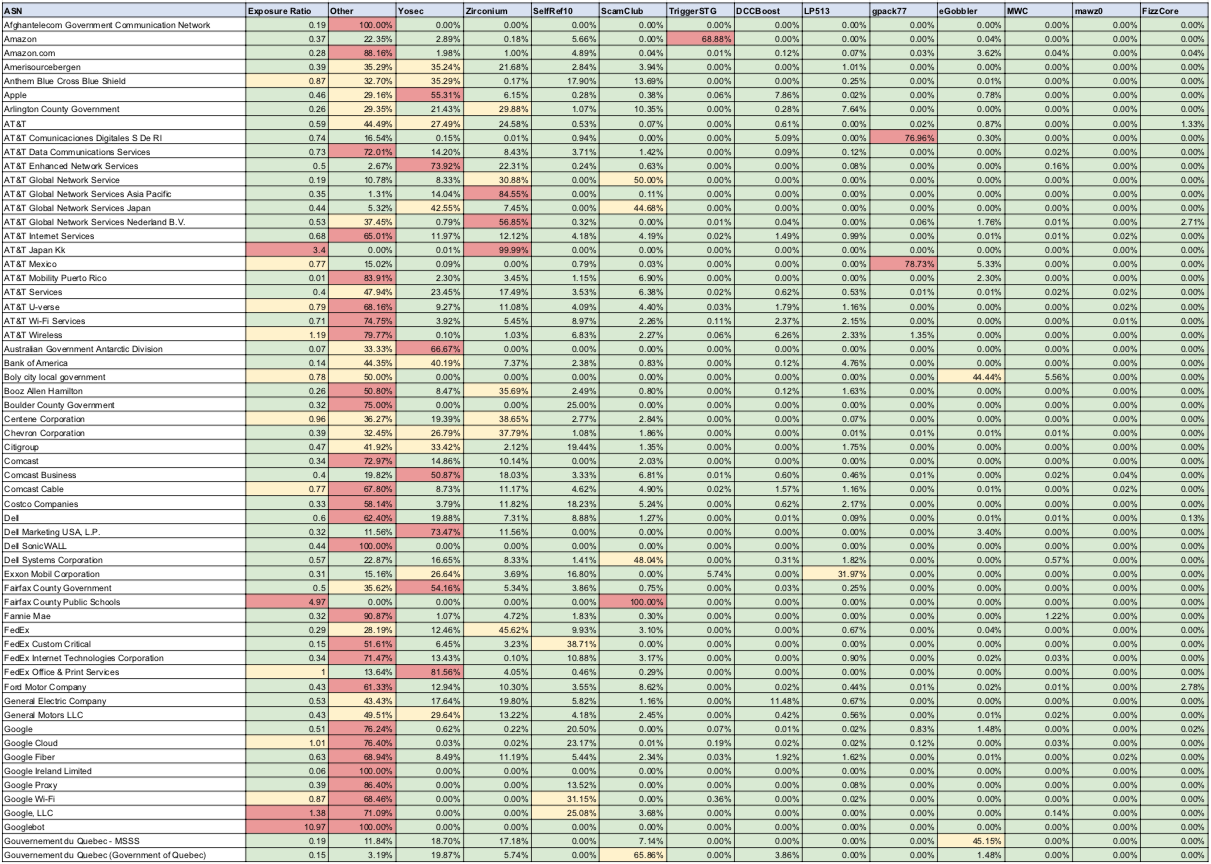
Malvertising’s Impact on Government Networks
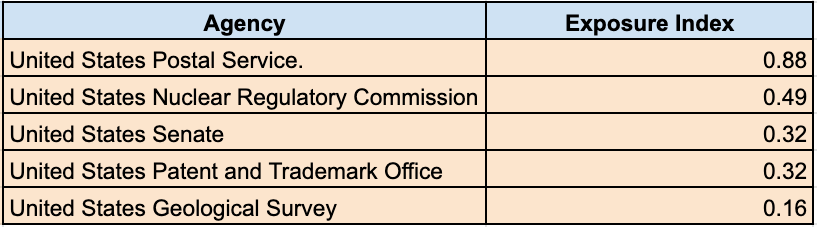
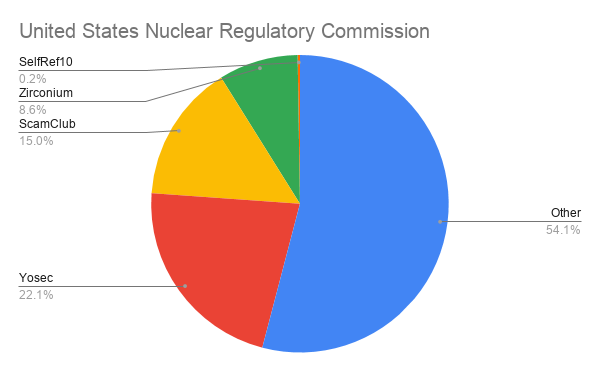
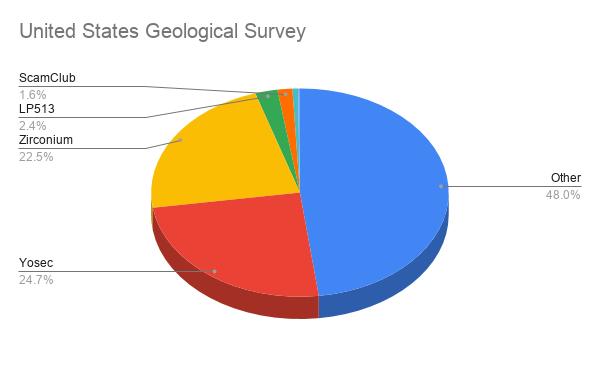
We can dive right into the data and take the top 5 government networks ranked by number of malvertising incidents during our time frame. Here are they are ranked by exposure index:
Unpacking The Findings
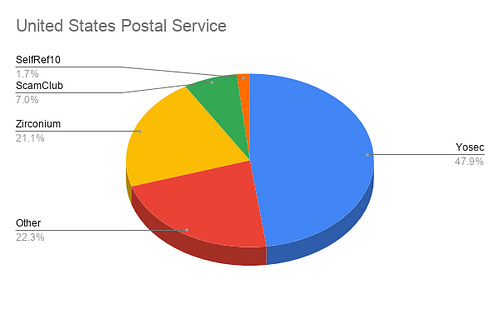
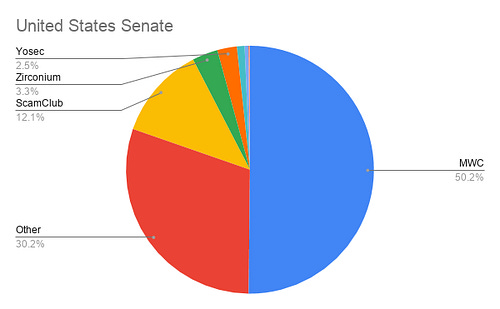
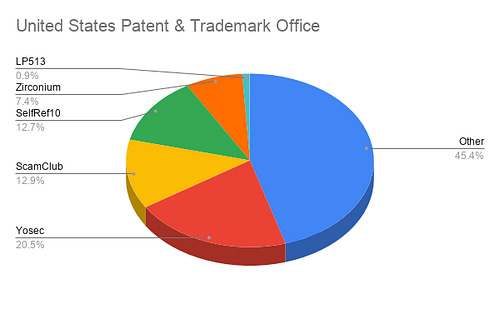
Fortunately, every organization on the list has an index below 1, which is exactly as we had hoped, but what immediately stands out is how the distribution of incidents by attacker varies so greatly from agency to agency.
What does it mean that the United States Geological Survey has been hit by Zirconium 22.5% vs the United States Senate’s 3.3%? Does it mean that Zirconium are actively attacking the Geological Survey with tech support scams?
The answer is probably not, however the fact that malvertising attacks are highly targeted is certainly responsible for this uneven distribution. For example, Zirconium payloads are often centered around tech support scams that are heavily targeted against outdated browsers.
Display advertising inherently has dozens of targeting criteria baked in for advertisers both good and bad to take advantage of, so of course it makes sense that a malicious campaign reliant on Windows virus warning messaging would be set up with targeting preference. Perhaps the machines on the Senate’s network are running browsers that are less attractive to Zirconium?
Our hypothesis is easily confirmed when we pull reporting by browser — 23% of traffic recorded from the Geological Survey is Internet Explorer, but only 1.6% for the Senate.
In addition, it’s especially noteworthy that malvertising campaigns are also heavily geo targeted and any given network infrastructure might have a geographic distribution that skews towards a region which might be more impacted during the time frame that we are looking at.
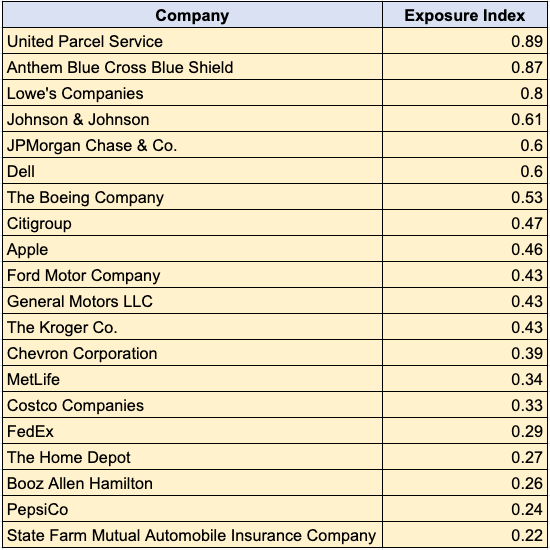
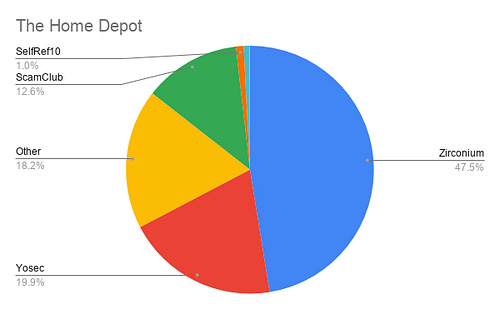
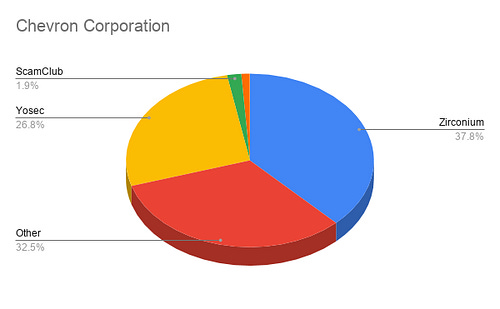
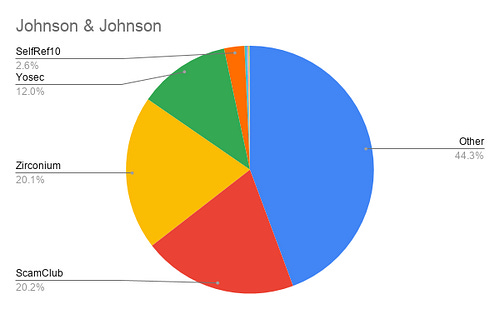
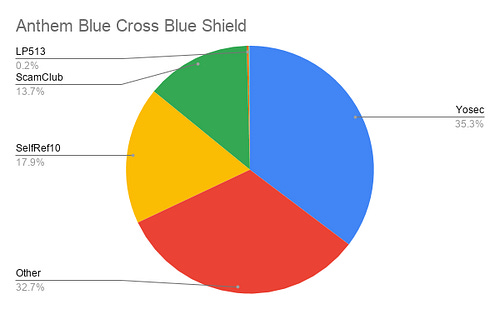
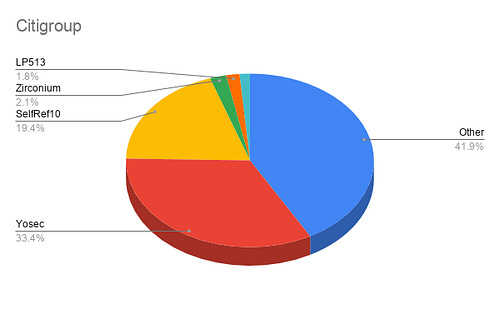
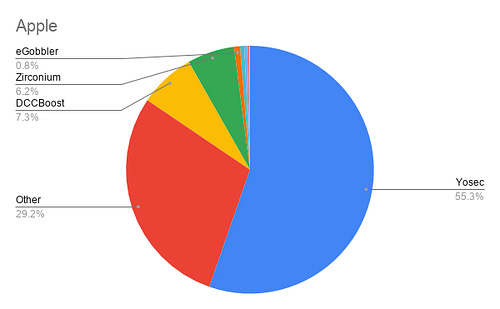
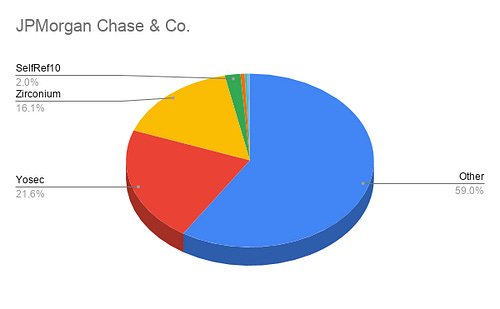
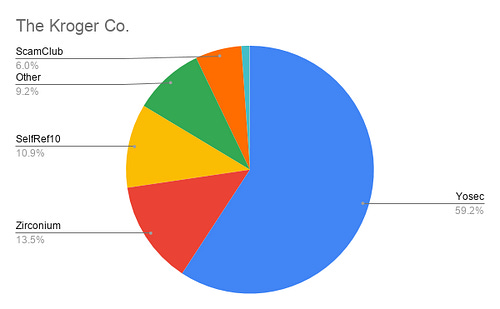
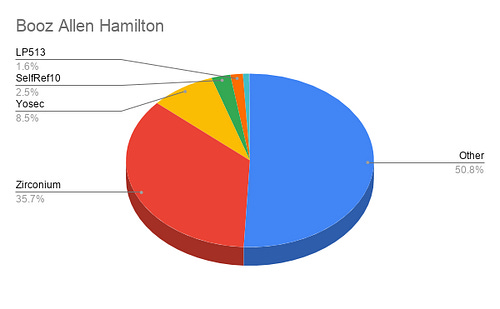
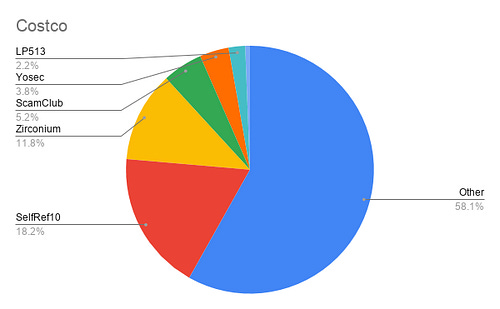
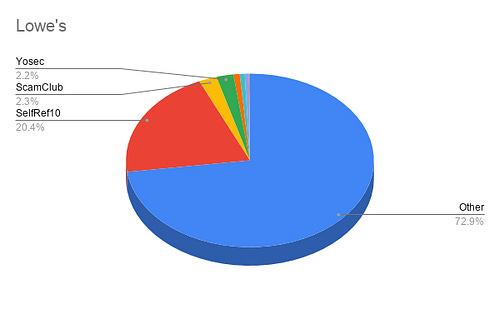
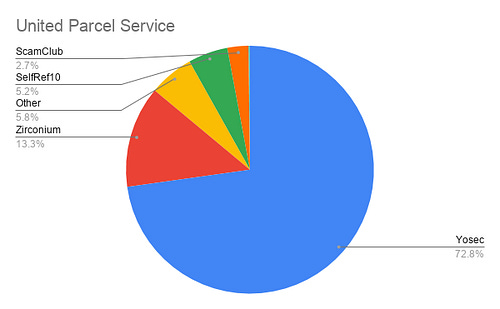
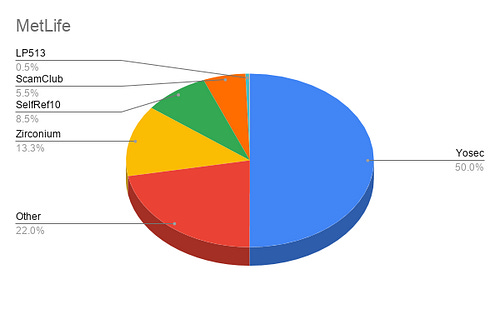
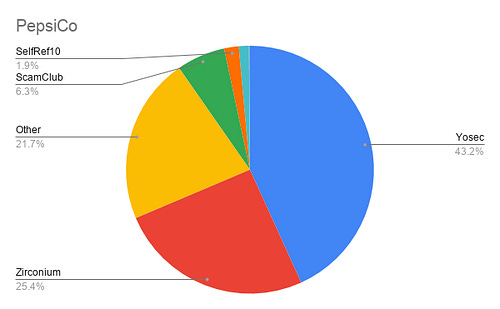
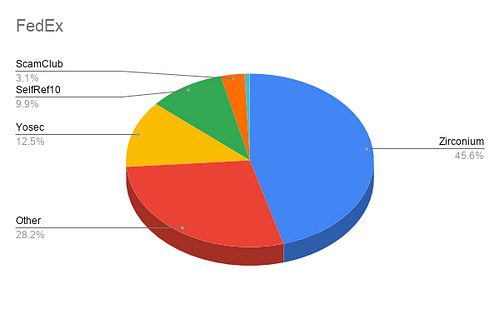
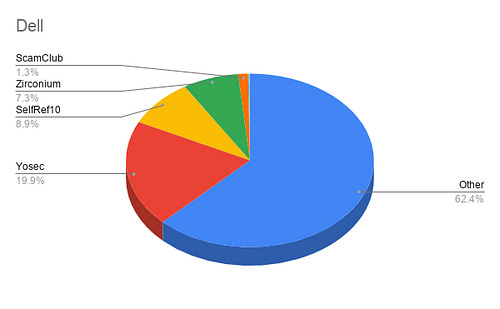
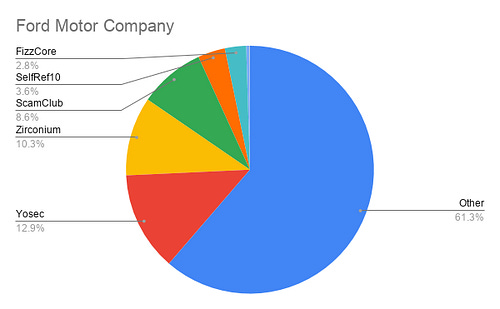
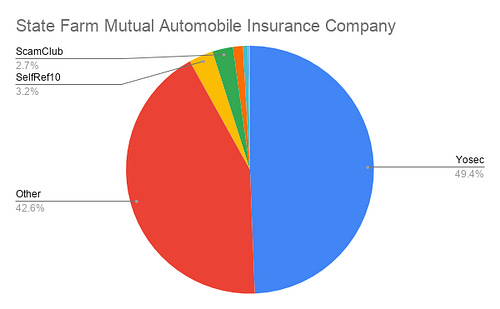
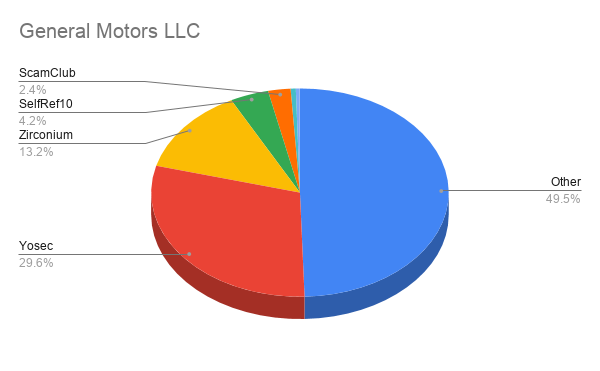
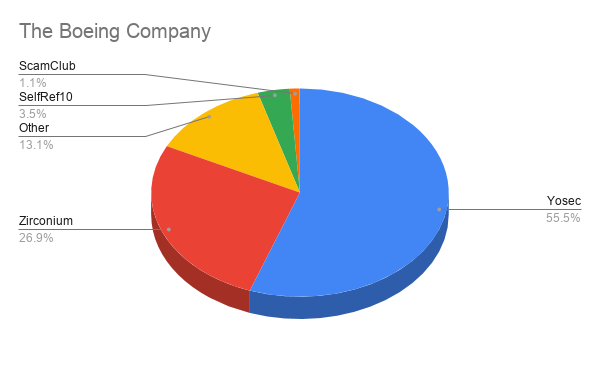
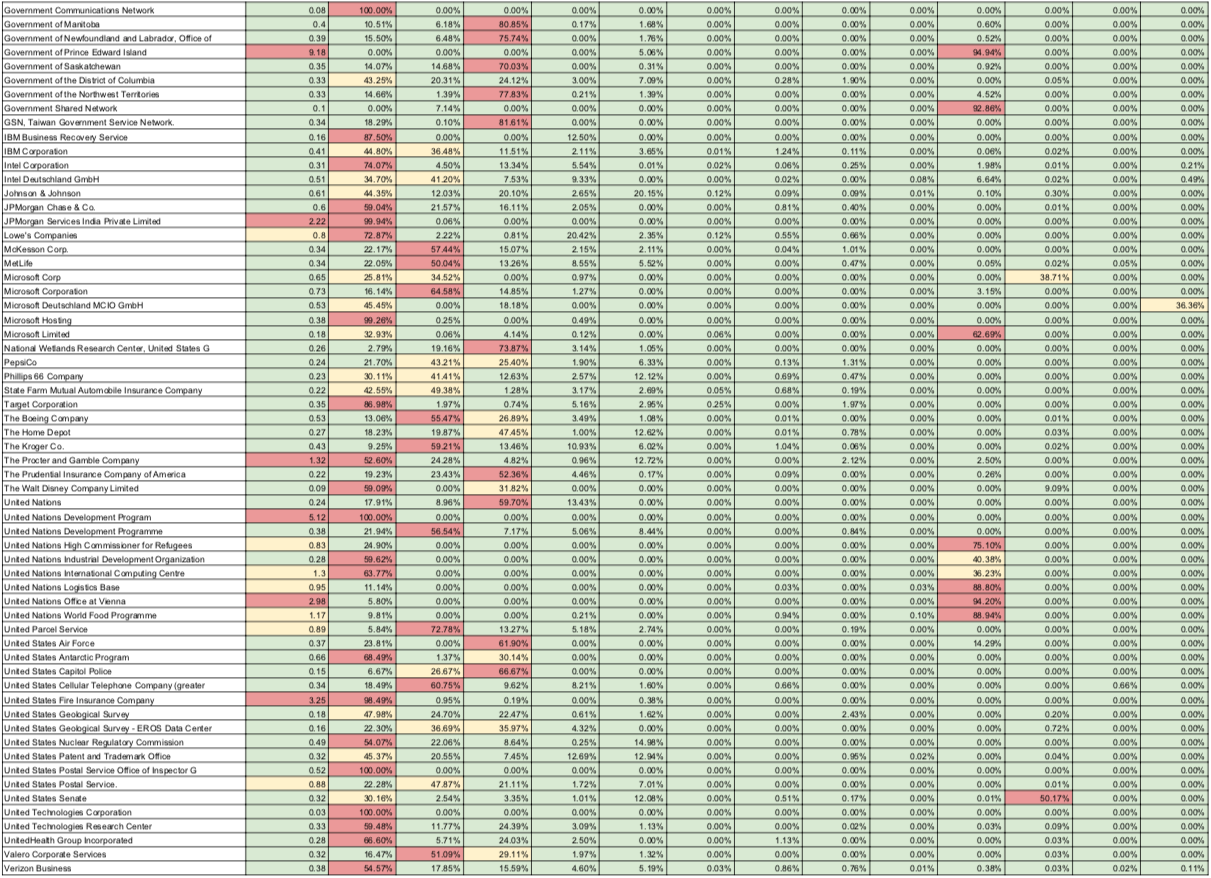
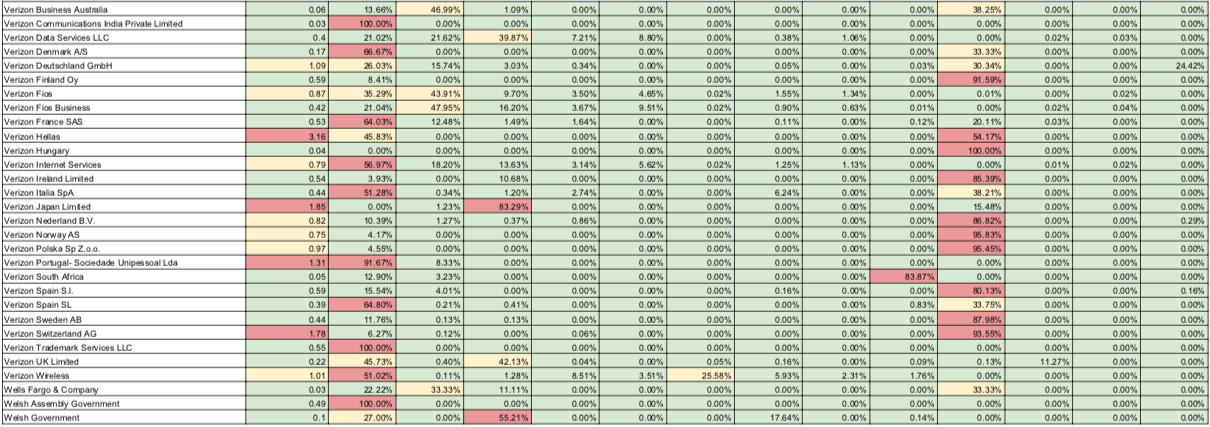
Impact On Fortune 100
For this section, we have singled out a variety of Fortune 100 companies, as well as a few household names. Again, our findings present that all of these major businesses have an exposure index that’s below average. It’s a refreshing finding, but not entirely unexpected.
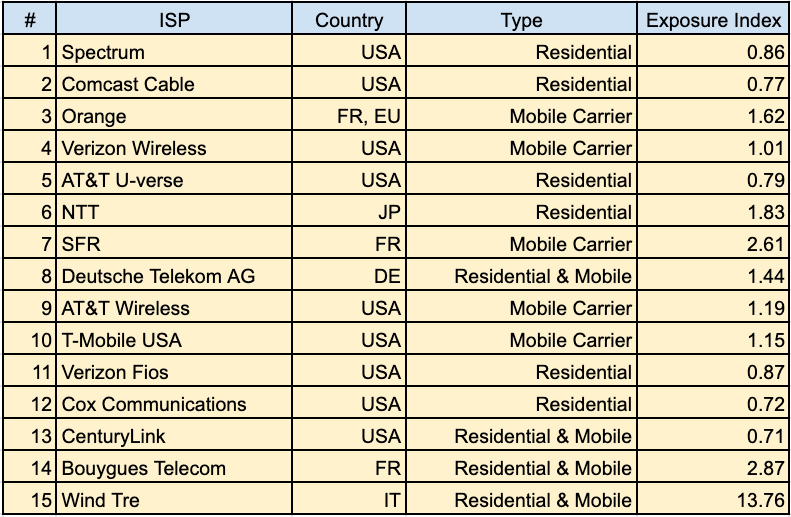
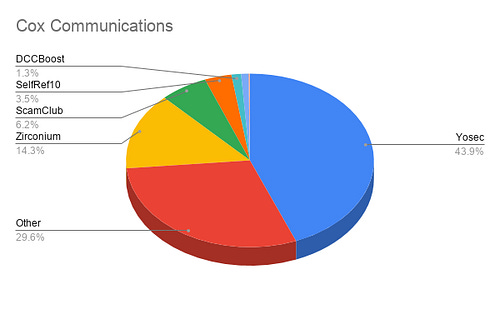
Malvertising Exposure By ISP
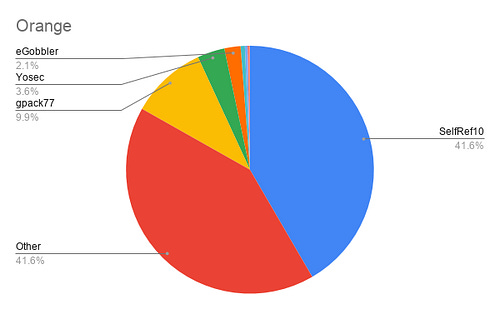
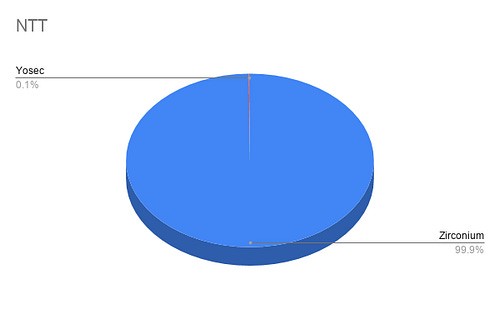
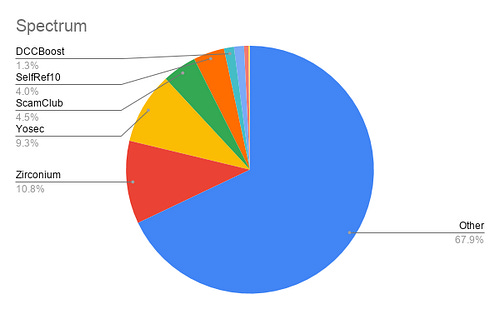
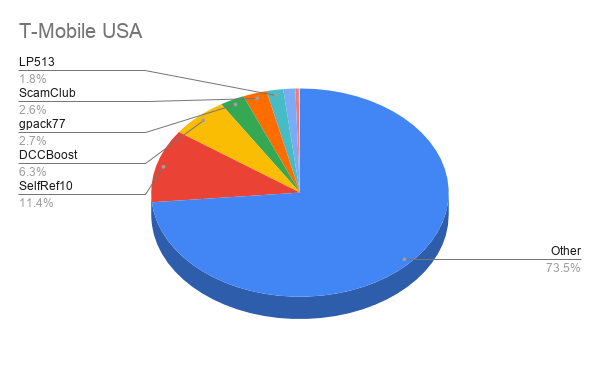
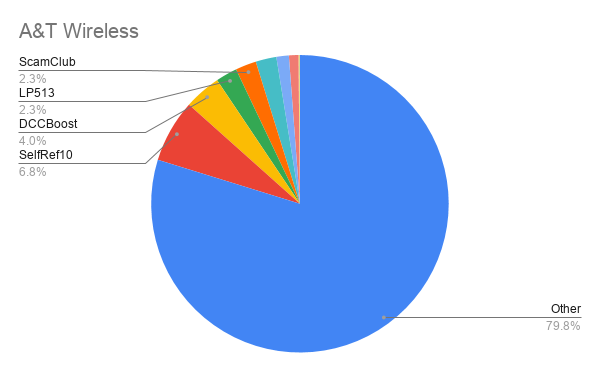
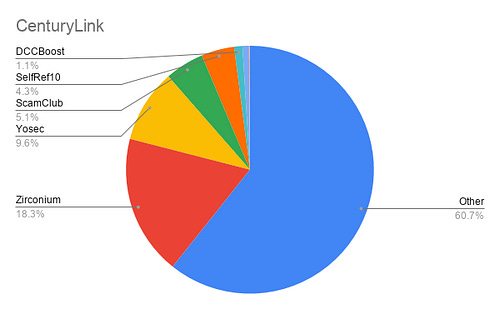
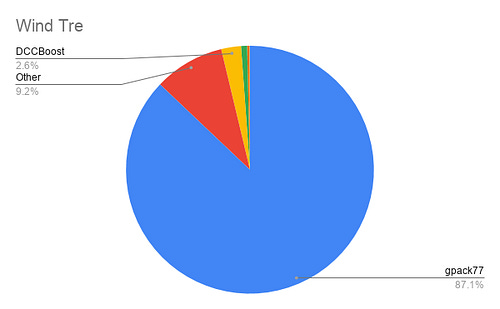
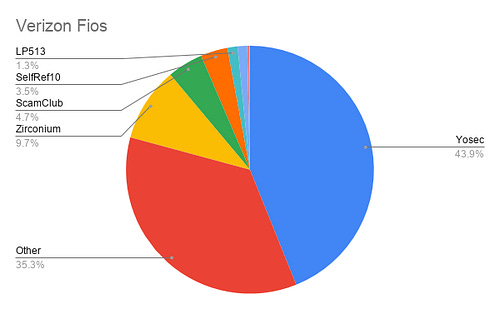
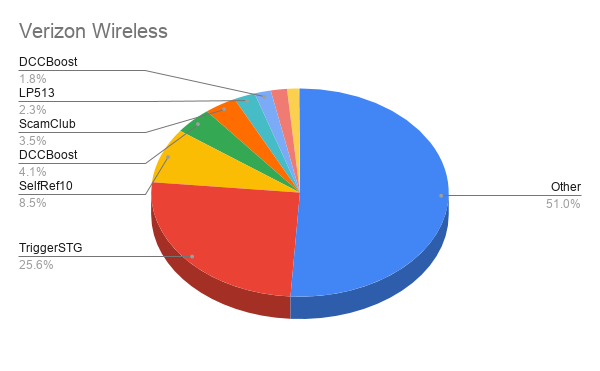
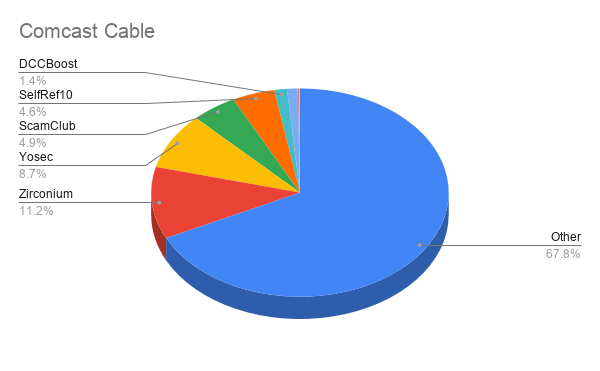
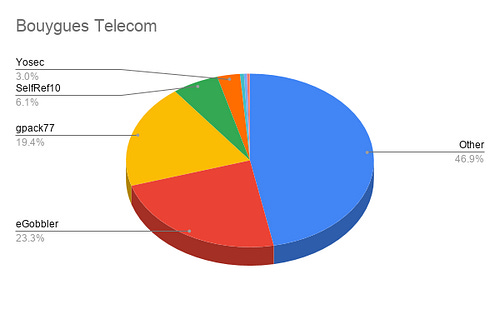
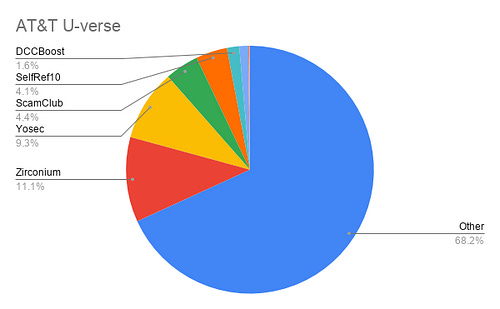
For this section, we zoom out a bit from the granularity we have presented so far and single out some ISPs and mobile providers. We curated the list below by sorting in order of most incidents for the time frame provided.
Unpacking The Findings
The ISP data provides new and interesting variance with both the exposure index and malvertiser breakdown. It also provides some telling context around the geo targeting tactics employed by these attackers.
Let’s look at the most obvious outlier here — NTT. The Nippon Telegraph and Telephone Corporation is among the largest telecom companies in the world, and of the incidents blocked on their network for the given time period, 99.9% are comprised of Zirconium malvertisements!
To date, we don’t see too many attackers going after Japanese audiences in this way, with US and EU getting the brunt of the action, but it’s an over-exploited market for Zirconium during this time frame.
We can make similar observations with Wind Tre — an Italian telecom operator. 87.1% of the incidents blocked on their network are attributed to gpack77. It’s clear that this attacker is quite underrepresented in the breakdown of most US based providers, but mobile users on this EU based provider are overexposed to their campaigns.
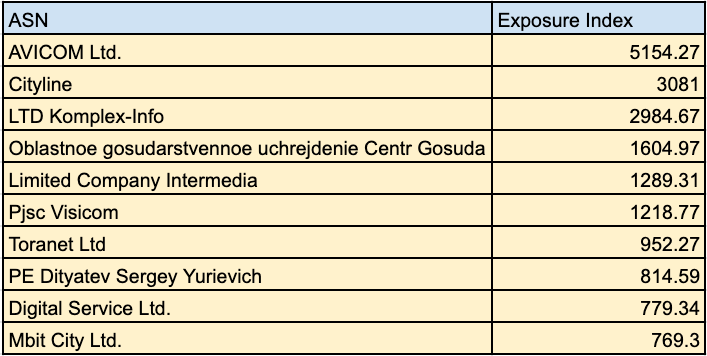
Bizarre Outliers
Then there are the confusing anomalies that sorely stand out. Provided below are the top 10 ASNs with over 1000 incidents ranked by exposure index. The majority of these based out of Russia and if we were to create pie charts for these, it would be a solid blue circle with 100% unattributed incidents.
In Conclusion
The findings above present a unique glimpse into how vulnerable some of these very high profile organizations are to the threat of malvertising. We found significant variance among ISPs, likely because these campaigns are designed to target specific audiences, and this targeting changes significantly over time as the attackers refine their strategies. We also found that in general, even the highest impacted government agencies and Fortune 100 companies are (to varying degrees) less exposed than the average corporate network — a significant finding considering that a compromise on one of these networks presents an impact that is magnitudes more severe than if the average internet user falls victim.
Appendix — A Curated Data Dump
Archive: This article was originally published on our Confiant Medium blog on February 24, 2020.