How File Hashes Fail As A Malware Detection Heuristic
In this blog post we take a trip downstream from malvertising delivery mechanisms and take a close up look at a fake Flash update landing page that was used to deliver desktop malware. We will take a look at some of the tricks these cybercriminals use in order to thwart detection on the wire. More specifically, we will see how malware campaigns are orchestrated to aggressively rotate landing page domains and serve binaries with unique hashes from unique sources on every single request.
The screenshot above and variations like it are probably familiar to anyone who has been online in the last 15+ years. Despite Flash having been on the decline for years and officially sunset as of 12/31/2020, landing pages like this are without question the most common vehicle for the spread of malware variants like Shlayer and Bundlore, both of which we have covered pretty extensively:
OSX/Shlayer new Shurprise.. unveiling OSX/Tarmac
Mac Spyware Shlayer is now dropping an entirely new malware we called OSX/Tarmac.blog.confiant.com
New macOS Bundlore Loader analysis
Looking at a recent Malvertising campaigns detected by Confiant realtime Malvertising detection engine, we stumbled…blog.confiant.com
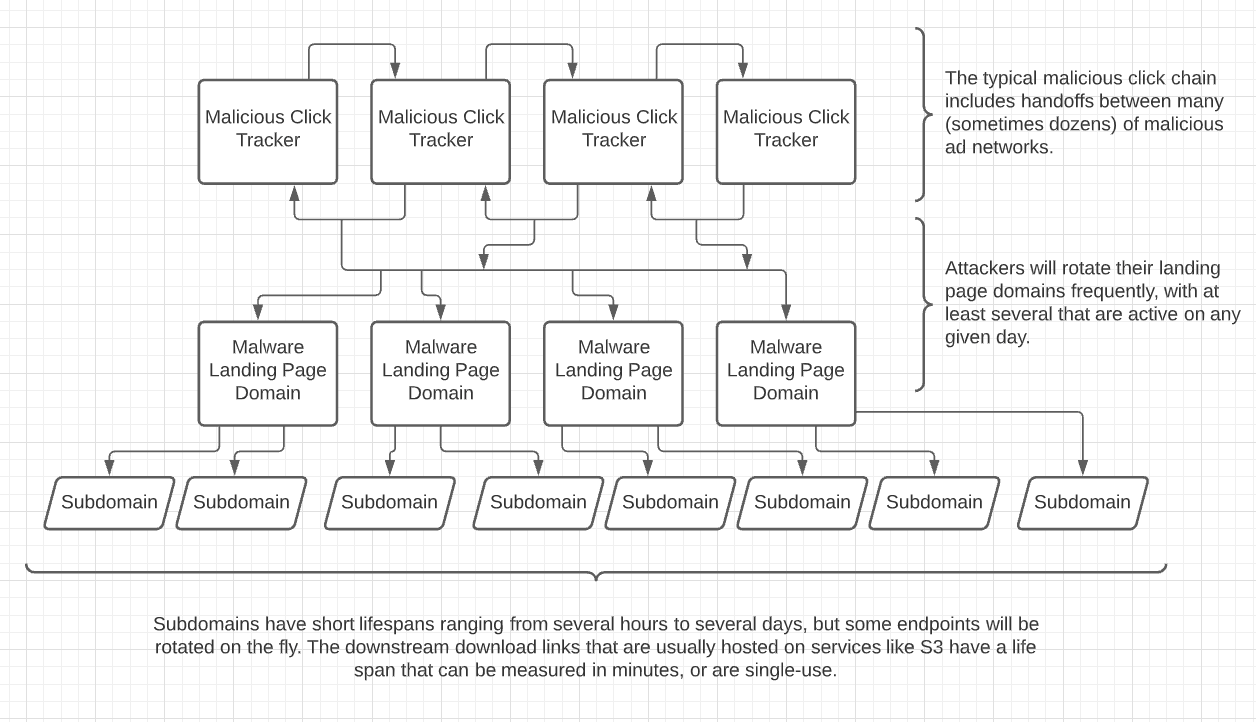
A typical malware campaign of this sort will rely heavily on an infrastructure that aggressively rotates domains, subdomains, and S3 buckets — either in real time or on a very frequent schedule (minutes). The more sophisticated players will also bundle or re-package their application on the go in order to ensure every single download has a different hash and file size.
Let’s dig in to our case study:
The landing page in question (screenshot posted above) was located at the following url:
https://softupdate[.]betterpath2updatinglink[.]work/sew?ftri=2qEIDmFngfGBxZafssyNEZwMRnAU20BU1EkcYRg2mUE.&cid=454444878915449034&sub=3193745#
Source of the html is can be found below:
https://gist.github.com/eliyastein/e69b3288a34251bdb8a2a37677a1682
And perhaps the most relevant piece of this whole html file is right here:
<a href=”/dl.php?ftri=2qEIDmFngfGBxZafssyNEZwMRnAU20BU1EkcYRg2mUE.&cid=454444878915449034&sub=3193745&conversion_id=16300013847132&app_id=100&lp_id=3281&v=revmacpkgnew3&stub_name=2030&v_id=&lpp=No+match” onclick=”showStep();” class=”download_link button” style=”text-decoration:none; margin-right:0; margin-top:40px; border:none; width:120px” >Download</a>Upon manual inspection, we click the download link and observe that we are redirected to an S3 bucket for the binary. After 2 or 3 manual downloads, we see that the location of the file (S3 bucket) is rotated, the file size is off by several bytes, and the dmg produces a different hash.
Curious as to what exact length the operators will go to try and obscure what they’re doing. We extract the download link and whip up a shell script to hit it repeatedly and log the results.
The script:
Some quick notes on the script:
We need to pass a long a valid User Agent for our request to be accepted.
We use the -I flag which only gives us the header, making it easy to extract the redirect to S3.
After leaving the script to run for ~2 hours we have aggregated a list of 2,272 unique paths on S3 spread across the following 15 unique buckets.
7fad0694-2b87-460c-8a49-8
b429
326ed53a-4f92-45f5-aa6c-e60
14a3574e
8b67323e-357a-4838-b330-c9ba7
a10becda-e785-41fe-950d-562081aba8f
87b0
9868d5df-ee7c-4eb2-87cd-49b17c9
5f6c2a7b-7
f86c2204-8a2c-40d2-8
9317dbdc-539
977a70d5-f4e
4c2e39d9-160c-44fd
8bcb
0d391009-f9The file sizes are mostly all unique as well:
$ ls -l | awk ‘{print $5}’ | uniq | wc -l
2216As well as the hashes:
$ for f in *; do shasum -a 256 $f; done | awk ‘{print $1}’ | uniq | wc -l
2270Detection Is Tricky
Though campaigns that leverage these tactics (and similar ones) have long been observed, the cybersecurity world still places a heavy premium on unique malware hashes and download links as IOCs, but ephemeral download links are entirely unreliable for detection.
Here’s a visualization of how any single malware campaign can quickly scale to a game of whack-a-mole against an epic number of urls.
Without a doubt, monitoring these campaigns at every layer can lead to crucial findings from a threat intelligence perspective, but reliable mitigation is better done upstream from the binary, the download link, and sometimes the landing page at a network level.
We find that real time analysis of malvertising chains is quite critical in the discovery of central points of infrastructure for these malicious campaigns that can be addressed more reliably. Usually these are pre-landers or campaign ID’s on unsavory ad networks that have malware affiliates on their networks.
IOCs — S3 Buckets
https://gist.github.com/eliyastein/e94ebef2f39e29495e0193065644924c
IOCs- DMG Hashes
https://gist.github.com/eliyastein/5b6fab50978919ad6d5c9c7ac4c4207e
Archive: This article was originally published on our Confiant Medium blog on December 6, 2021.