Malvertising Attack Hijacks 300 Million Sessions Over 48 Hours
Nov 12th Malvertising Attack Serves Adult Content and Gift Card Scams
Overview
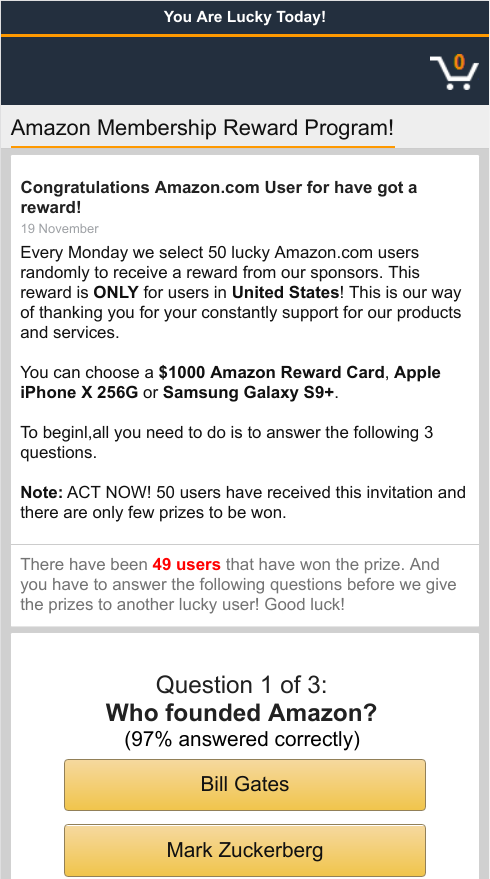
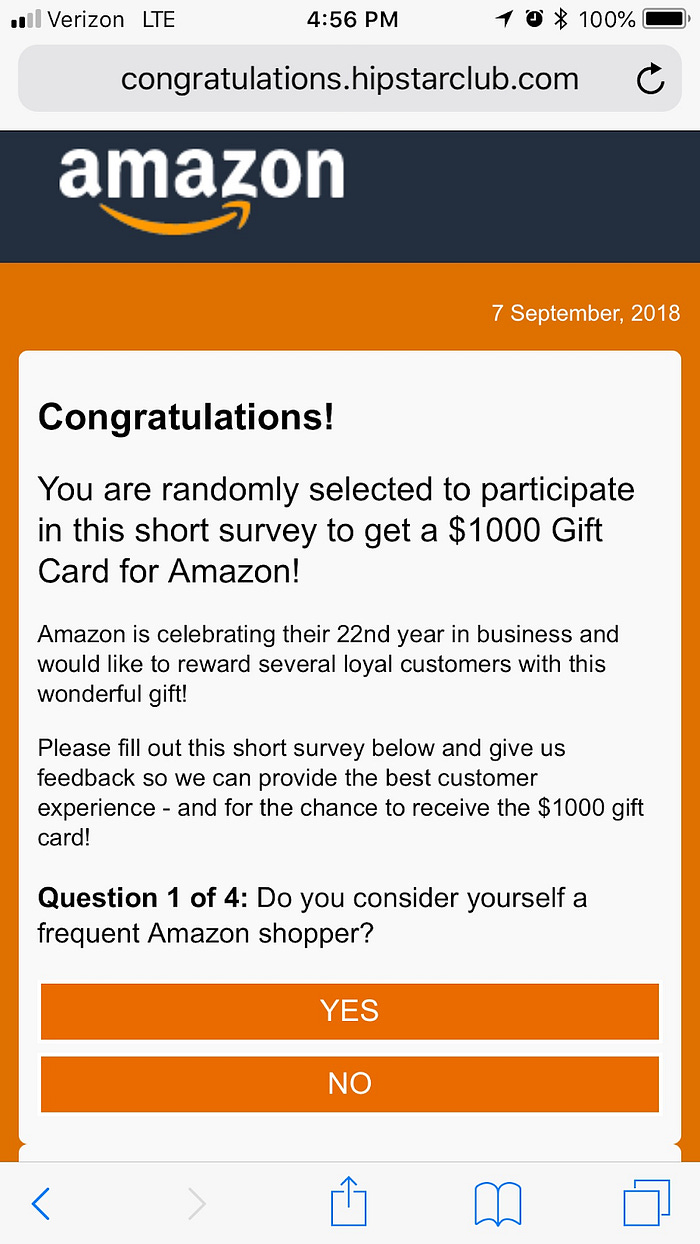
The ad unit manifests forceful mobile redirects that are then being used for various malicious activities, such as monetizing by redirecting the hijacked session to adult content and gift card scams.
The click through URL for many of these campaigns was: play.google.com (google play app store)- safe to assume that these campaigns were impersonating legitimate app download campaigns.
Served through a top 5 advertising exchange - 57% of our publisher clients working with this ad exchange were impacted.
Targeting United States visitors (99.5% of hits)
Targeting iOS devices (96% of hits)
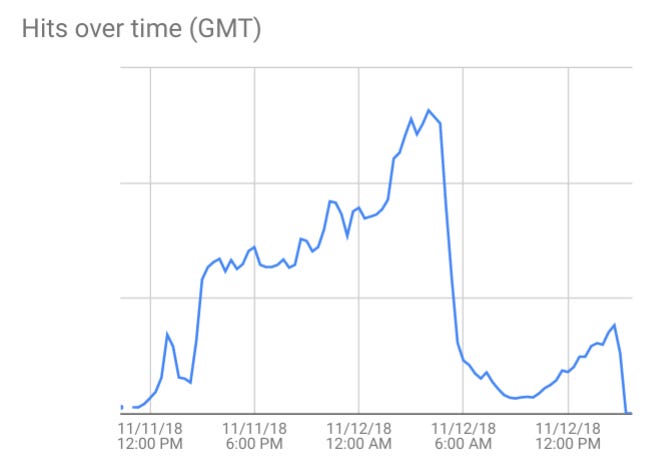
Confiant immediately identified the threat on Sunday night (Nov 11th) and started blocking it from affecting visitors on our clients’ websites.
Recent payloads
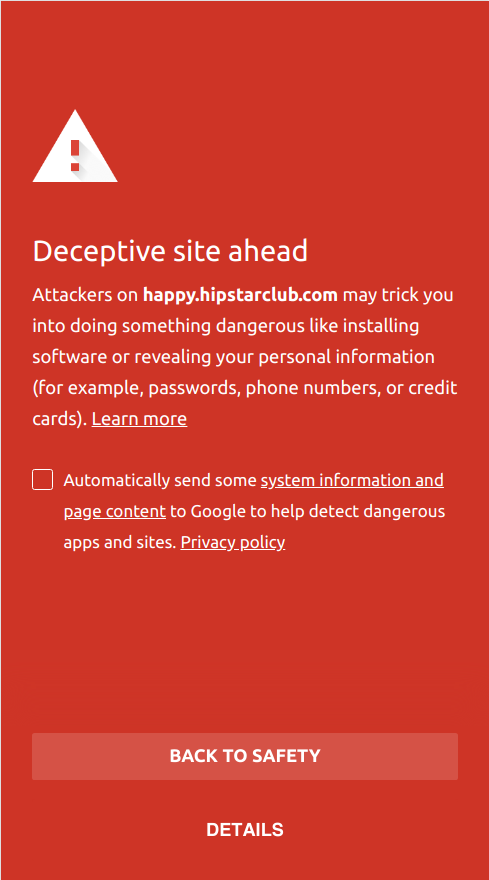
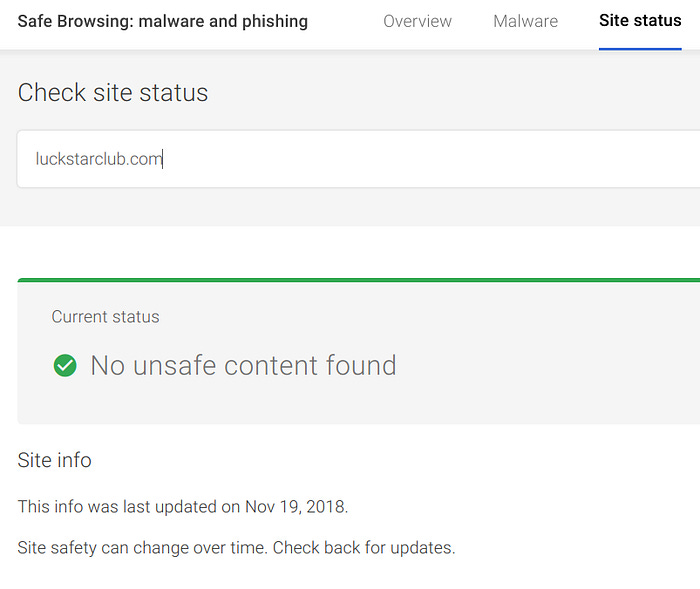
Security Vendor Detections
Google SafeBrowsing and other security vendors have been late at reporting the landing pages as malicious. The latest domain used in the scheme (luckstarclub.com) has been flying under the radar for weeks (not detected by either Google SafeBrowsing or VirusTotal).
happy.hipstarclub.com
https://www.virustotal.com/#/url/b5e1a4a04037a5dba111987f927e37df7b6861593e40f647239ba82dbee4b1de/detection
(2 / 66)
happy.luckstarclub.com
https://www.virustotal.com/#/url/46832020f01bc0bf996b74aaec278447f01fe3f92e41ab10d6a7370a3b703671/detection
(0 / 66)
Landing pages
Fake Amazon offer
Adult content
New domain — luckstarclub
Highlights and takeaways
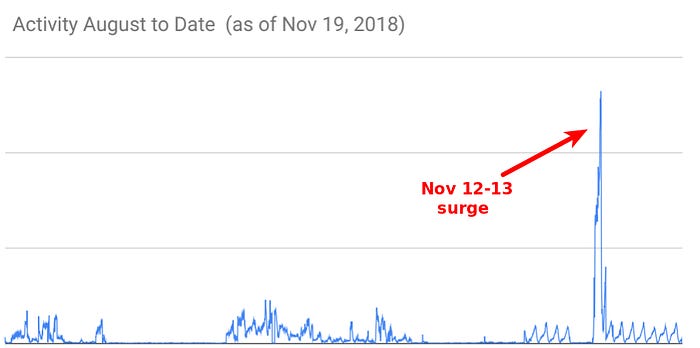
Confiant’s telemetry monitored the delivery of this malvertising campaign from Sunday to early Tuesday, roughly 48 hours. During that time, Confiant recorded and blocked over 5 million hits. The total amount of impressions served to publishers left without Confiant’s protection is estimated at over 300 million impressions during this 48-hour period. By comparison, the Zirconium group was responsible for only one billion impressions throughout a whole year (2017).
Previously, the attacker had been actively laying the grounds since August of this year, but with much lower visibility to tier-1 publishers, via smaller exchanges
The attacker historically targeted the US, but also ran separate geo-located malvertising campaigns. For example, an on-going campaign exclusively targeting Australia and New Zealand has been active since Oct 20.
FAQ
Confiant monitors all programmatic ads that run through our platform for the presence of code associated with malvertising, oftentimes forced mobile redirections. The incident in question is one such creative that we flagged and started seeing / blocking at a scale of 5mm impressions in ~48 hours.
Our system performs advanced automated analysis on creative code. This analysis happens in real time and is able to recognize if certain known malicious behaviors are being triggered. When needed, we perform an additional manual analysis on the creative code. Our security team will reverse engineer any code associated with the creative in order to get a deeper understanding of the attack vector and the payload.
What type of sites were affected?
A variety of content sites were affected by the campaign. Specifically, 57% of publishers working with this top-5 ad exchange were impacted according to Confiant’s data.
What technical information do they have?
Sophisticated bad actors will often try to determine if their campaign is being displayed in a virtual environment or to a real user. In this case, among other things the ad had code that tried to identify whether or not it was running on a real user’s device.
What attacks/malware were instigated/spread by the attack?
Forceful redirection to fake “you’ve won a gift card” or adult content landing pages. These pages typically try to phish visitor data in order to commit affiliate marketing related fraud and or steal personal identification data.