Malvertising Threat Actor “Yosec” Exploits Browser Bugs To Push Malware (CVE-2021–1765, CVE-2021–30533)
Most threat actors that operate via ad tech have embraced an operational shift over the last 2 years, leaning heavily into cloaked clickbait and away from forced redirects and pop-ups.
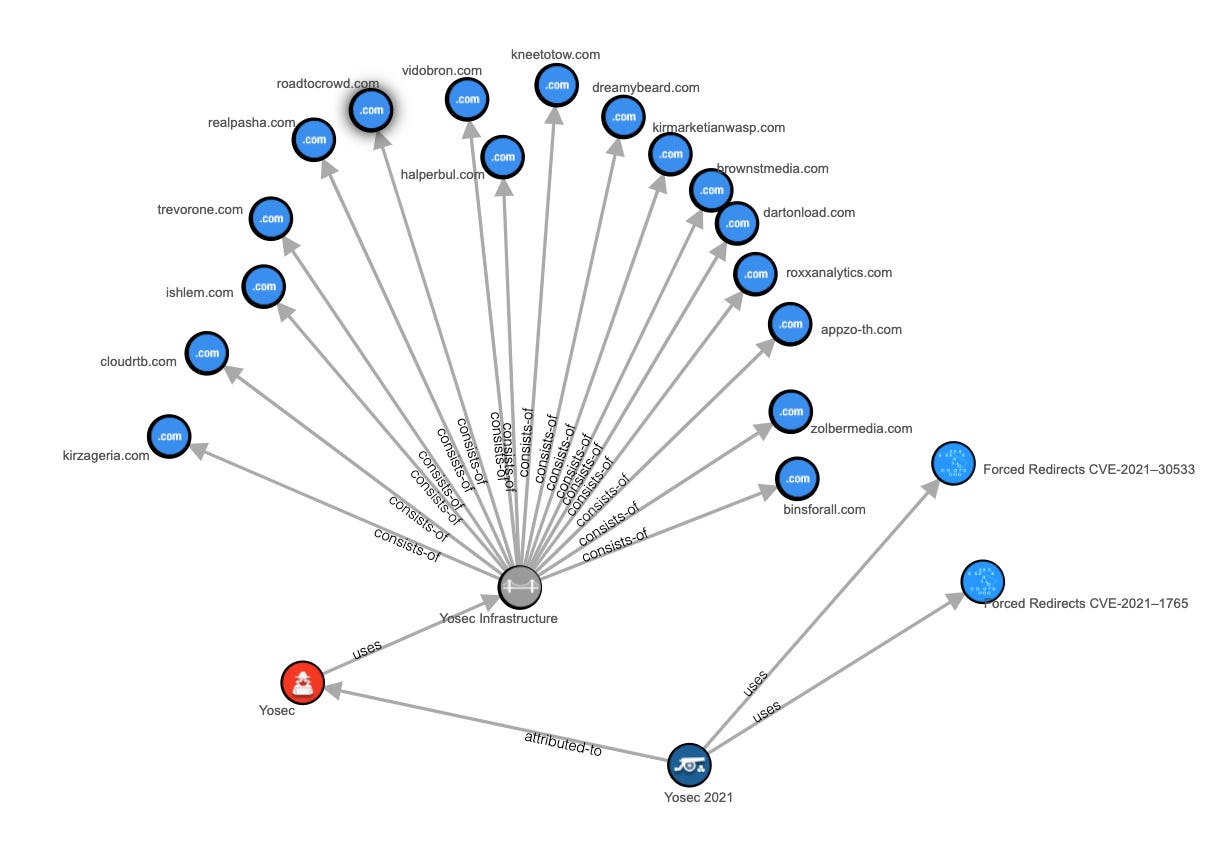
Despite this growing trend, some malvertisers, particularly those that push malware, continue to hang on to redirect tactics. Among the players that stuck it out, Yosec were one of the more consistent groups that ran large scale, high impact campaigns throughout 2020.
Much of the overall decline in disruptive redirects is due to several factors. First, ad tech security overall has matured greatly in the last four years. In addition, web browsers have made significant improvements around functionality that requires user activation from within iFrames — forced redirects are a prime example.
In spite of these improvements, cybercriminals often remain a step ahead with tricks and tooling to circumvent these measures as they always have. Case in point are the multiple browser bugs that we have reported to be abused by malvertisers in recent years:
This latest exploit was discovered as part of a raging malvertising campaign that rocked the ad tech ecosystem on November 3rd, 2020 with an estimated 100MM ad events impacted on that day alone.
Here’s the redirect payload that piqued our curiosity:
When it comes to nefarious JavaScript, it’s common to see a lot of things that simply don’t make sense, usually red herrings used to obfuscate the code. However, if you operate under the assumption that everything is intentional and dig deep, you might find that some of the confusing code is far from random.
As always with unique redirect payloads, we run a comprehensive suite of tests which includes analysis of their efficacy in seeming impossible environments like cross-origin iFrames, sandboxing, etc.
In this case, we found the payload effectively bypasses iframe sandboxing in both WebKit and Chromium based browsers.
Yosec Today
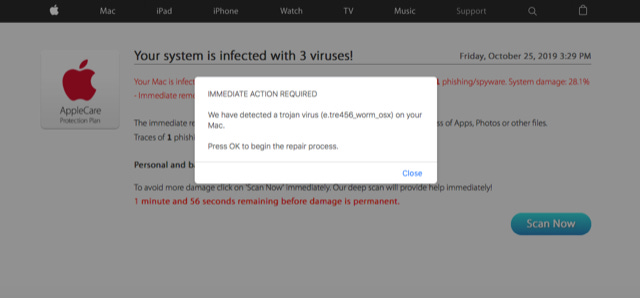
The malvertising group continues to stay active throughout 2021 at steady, but mostly modest volumes, smuggling redirect payloads behind benign looking display ads and using their own infrastructure for serving the creatives like this example from June:
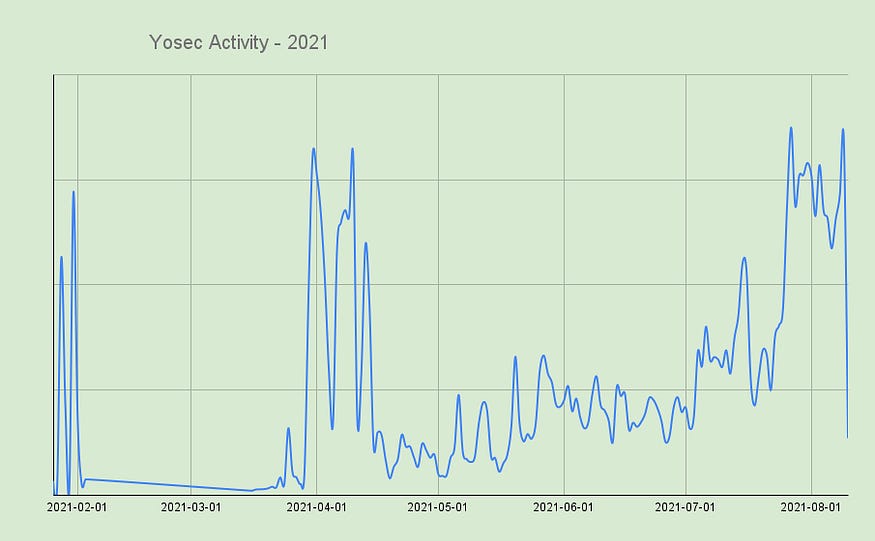
We can get a sense of their day-over-day cadence by graphing daily volumes over the course of recent months. The peaks on the chart represent in the ballpark of ~600K ad impressions in the wild.
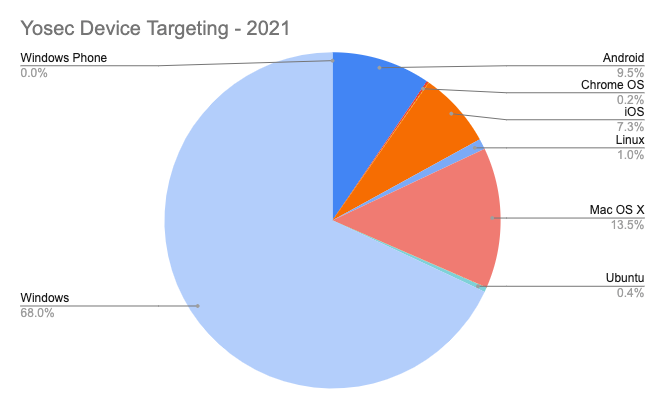
And of course, since Yosec typically pushes malicious applications, they will target mainly desktop operating systems:
Final Thought
Yosec is but one example of a sophisticated criminal enterprise that leverages digital advertising technology as a vector to deliver dangerous payloads.
In order to maximize the impact of such attacks, these malvertisers are very keen on exploiting any browser bugs that have broadened the scope of potential victim devices.
Iframe sandbox and user activation bypasses are ripe targets for these attackers, and while browser vendors do make an earnest attempt to patch these quickly, new functionality is constantly being introduced with every release — potentially increasing the attack surface for these types of abuses and increasing the severity of these already disruptive malware campaigns.
Timeline
Nov. 3, 2020 — Confiant detects a massive Yosec campaign with unique iframe sandbox bypass exploit.
Nov. 4, 2020 — Chrome team and Apple teams are notified.
Jan. 22, 2021 — Apple issues Webkit fix, CVE-2021–1765 is assigned.
Mar. 1, 2021 — Patched in Chrome.
May 24, 2021 — Chrome CVE-2021–30533 assigned.
References
https://bugs.chromium.org/p/chromium/issues/detail?id=1145553
https://support.apple.com/en-us/HT212147
IOCs (Last 6 months)
*.vidobron.com
*.zolbermedia.com
*.appzo-th.com
*.cloudrtb.com
*.brownstmedia.com
*.dartonload.com
*.realpasha.com
*.kneetotow.com
*.halperbul.com
*.kirzageria.com
*.trevorone.com
*.roadtocrowd.com
*.roxxanalytics.com
*.ishlem.com
*.marketianwasp.com
*.dreamybeard.com
*.parmaads.com
*.binsforall.com