Nov 22–25 Attack of The Cyber Turkey
Overview of Thanksgiving holiday weekend malvertising activity
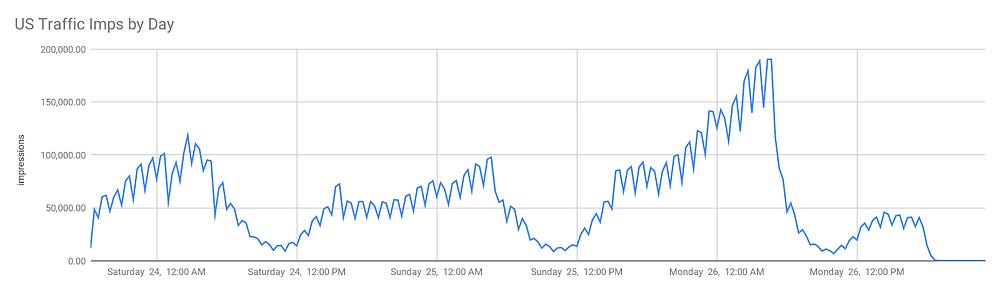
During the holiday weekend, Confiant tracked and protected its clients from a massive malvertising spike, detecting and blocking 20 million malicious sessions across 3 distinct attacks (The Gobbler, Balk Friday and LLTag), each on different tier-1 ad exchanges.
We do not have precise scale measurement for these concurrent attacks but the combined impact is multiple times higher than the surge we measured on November 12, just two weeks earlier.
Although these specific attackers have been around for months, they concentrated their efforts over the holiday weekend, successfully betting that they would more easily break through during a time when ad operations teams are less available to troubleshoot security issues.
Campaigns like this have a massive negative impact on publishers, brands, and consumers. The bulk of these scams exists in order to commit affiliate fraud and phish users to steal personal identification data. Since brands ramp up their spending during the holidays, malvertising has a bigger overall impact on these peak periods.
The malvertisers’ business model is amplified by the holidays as the message is more likely to carry across to unsuspecting consumers who will fall for the scam. With more folks shopping online than usual, this enables the scammers to maximize their reach.
How do these hijacks work?
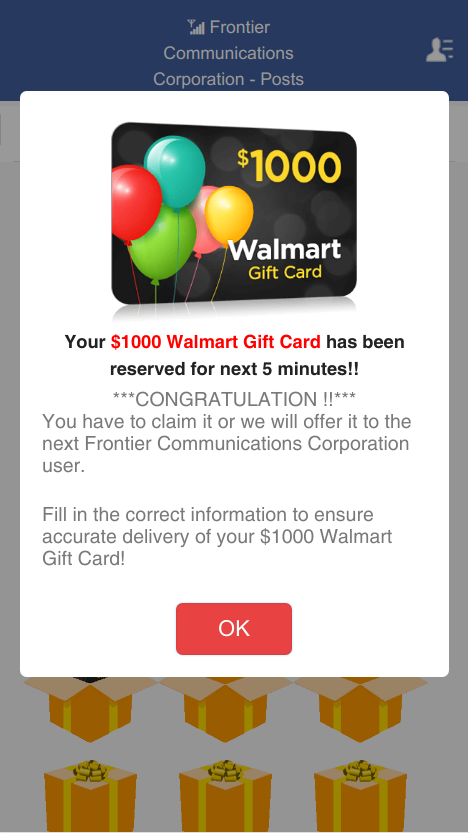
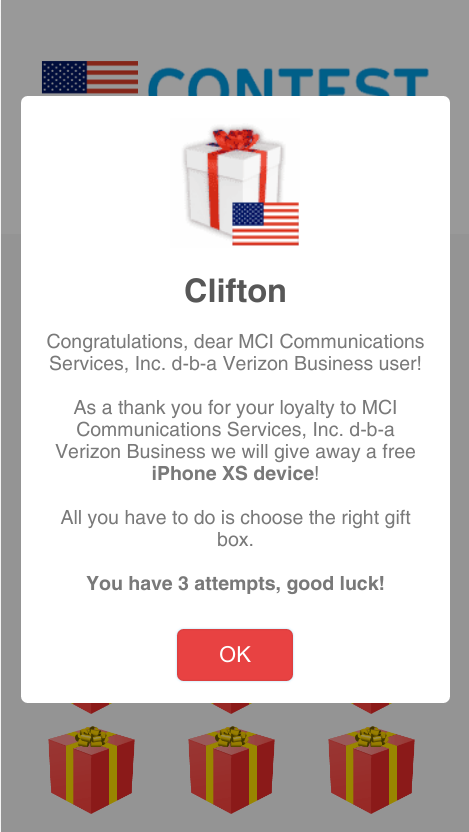
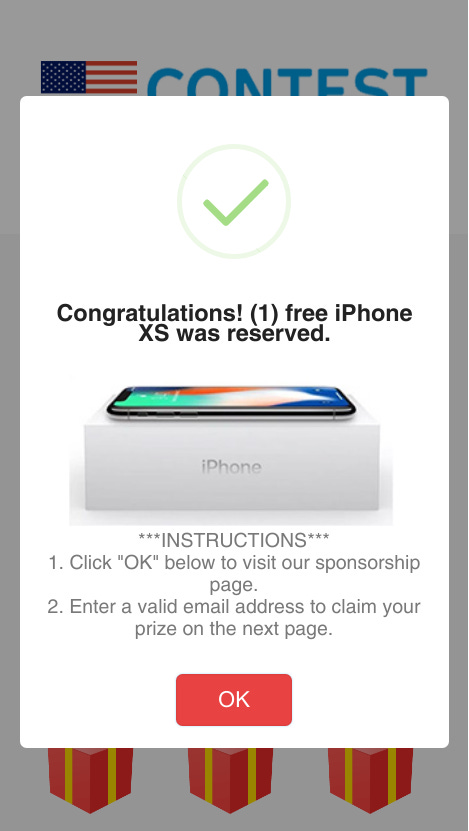
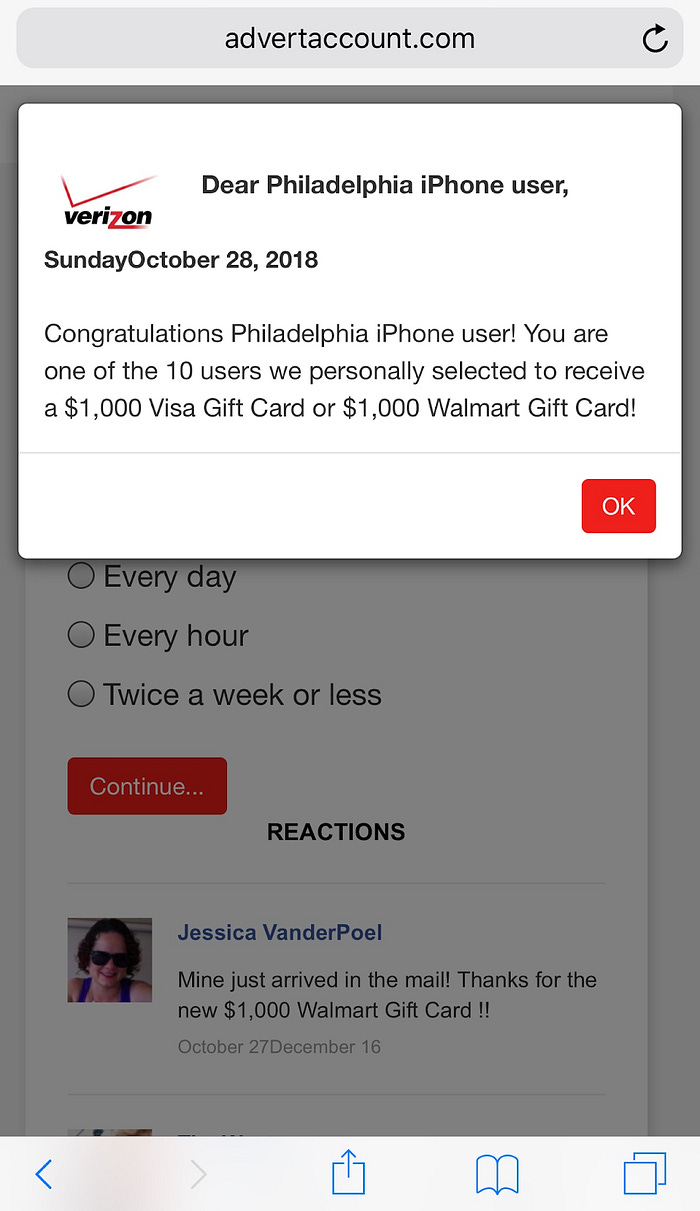
Broadly speaking, any website monetizing with ads introduces this risk to their users. From a user perspective, as they visit a web page, the malicious ad executes malicious Javascript to trigger a forceful redirection without user interaction. The user is presented with a fake ad promising a chance to win a $1000 or the latest iPhone. Like all advertisers, the malvertisers goal is engagement. Attackers piggy back on the trust established by websites with their users and leverage that to compromise users devices or steal personally sensitive information.
How do these attackers evade detection so effectively?
The ad industry attempts to weed out malicious ads using a mix of automated and manual controls. It is not economically feasible to test the millions of ad creatives running through the ecosystem using real user devices (i.e. iPhones). Attackers use this to their benefit and look for technical details that make an iPhone unique and difficult to replicate in an automated test environment in the cloud. In the cases occurring on Thanksgiving week-end, the criminals used Javascript APIs to look up device-specific information like the GPU chipset used by the device. In the cloud, automated scanners are obviously not equipped with the Apple A11 or A12 custom-made GPU chipsets.
How did Confiant spot it?
Confiant’s system performs advanced automated analysis on the creative code at the point of delivery (to users in their browsers or on their device). This analysis happens in real time and is able to recognize if certain malicious behaviors are being triggered. The automated methods are supported with additional automated scans and expert manual analysis of the code. Our security team reverse engineers any code associated with the creative in order to get a deeper understanding of the attack vector and the payload.
“The Gobbler”
Malicious behaviour: Triggers a forced redirect
This attack (targeting the United States exclusively) borrows a creative from Deutsche Bank normally aimed for the Netherlands market.
The HTML5 creative is modified to host an obfuscated malicious code snippet. Specifically, the Greensock library is altered deep inside the minified code, in order to make manual inspection extremely challenging.
Payload: Walmart gift card landing page
Duration and Timing
Impact
12.5 MM hits
Targeted Audiences
iOS in the US
“Balk Friday”
Malicious behaviour: Triggers a redirect
Fake ad creative:
https://www.otto.de/
Payload: free iPhone landing page
Timing
2 days from Nov 23 to Nov 25
Impact
3.9 MM hits
Targeted Audiences
iOS (84%) Android (16%)
USA, Germany, Australia, Taiwan, France, India
This fake black friday creative was hastily set up. The malicious code was hosted under a “balck friday” URL.
https://d3drr4gm70soyv.cloudfront.net/otto/balck/friday/
“LLTag”
Malicious behavior: forced redirect to gift card scams
Served from now defunct domain lltag.com followed by spreedtag.xyz
Using WebGL APIs in order to evade detection / fingerprint devices
In this specific campaign, the attacker borrowed multiple ad creatives to deliver the payload. An example advertiser was
https://store.roosterteeth.com
(which is not controlled by the malvertiser but serves as a placeholder to appear legitimate on inspection).
Like many other campaigns, this one involves a self-served DSP based out of a non-tier 1 geography and well implanted across multiple ad exchanges.
Payload
Timing
This specific campaign was active from November 22 to November 26.
Impact
3.3 million hijacked sessions in 4 days through the Thanksgiving week-end
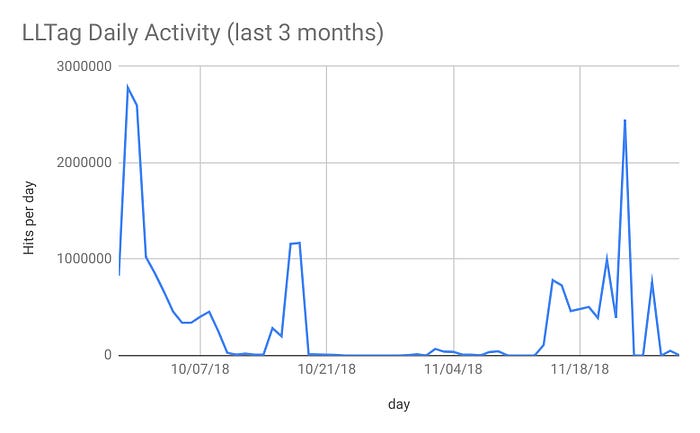
Aside from this large scale incident, LLTag has been very active over the last 3 months as Confiant recorded 22.3 million hits through this period.
Targeted Audiences
United States, Great Britain, Germany, Canada
iOS (61%) Android (39%)