Revealing How "The Dandelion Group" Leverages Multiple Layers Of Cloaking To Run Ad Fraud Campaigns
This blog post will unveil the inner workings behind a persistent ad fraud operation that relies heavily on cloaking in order to siphon dollars from display and native advertisers. We will also explore the murky boundary between malvertising and ad fraud.
verb: cloak
to conceal content served (by a website or web server) based on the entity that requests it
The Dandelion Group, so named after their heavy usage of the domain weedlio[.]com often enter the display ad eco-system through a seemingly traditional ad tag (as most fraudsters do). The tag looks a little something like this:
It’s subtle, and typical enough to go unregarded, but there’s some misdirection going on. It’s a lot easier to see if we zoom in on it and deconstruct it:
<iframe src=”about:blank” id=”aXH5y3BEBJ3_RlPmTJxOQuw” frameborder=0 marginwidth=0 marginheight=0 scrolling=no allowtransparency=true width=300 height=250></iframe><script type=”text/javascript”>
var all_urls = [’hxxps://weedlio.com/g/2jrVhZ0’]
, all_urls_length = all_urls.length
, random_url_number = Math.floor(Math.random() * all_urls_length)
, random_url = all_urls[random_url_number];
document.getElementById(”aXH5y3BEBJ3_RlPmTJxOQuw”).src = random_url;
</script>The JavaScript here is completely absent of any practical relevance. It’s a red herring for the guise of ad tech legitimacy, packaged to resemble a cache buster that we are all used to. However, the random number generated here is never applied and the entire 6 lines of code might as well be written like this:
document.getElementById(”aXH5y3BEBJ3_RlPmTJxOQuw”).src = ‘hxxps://weedlio.com/g/2jrVhZ0’;All this does is set the destination of the ad iframe. Let’s render it:
On the surface we’re confronted with a native style ad, but of course there’s more going on… and what’s up with that rumbumptious[.]com domain? Let’s check what the iframe is actually serving up when this creative wins a bid:
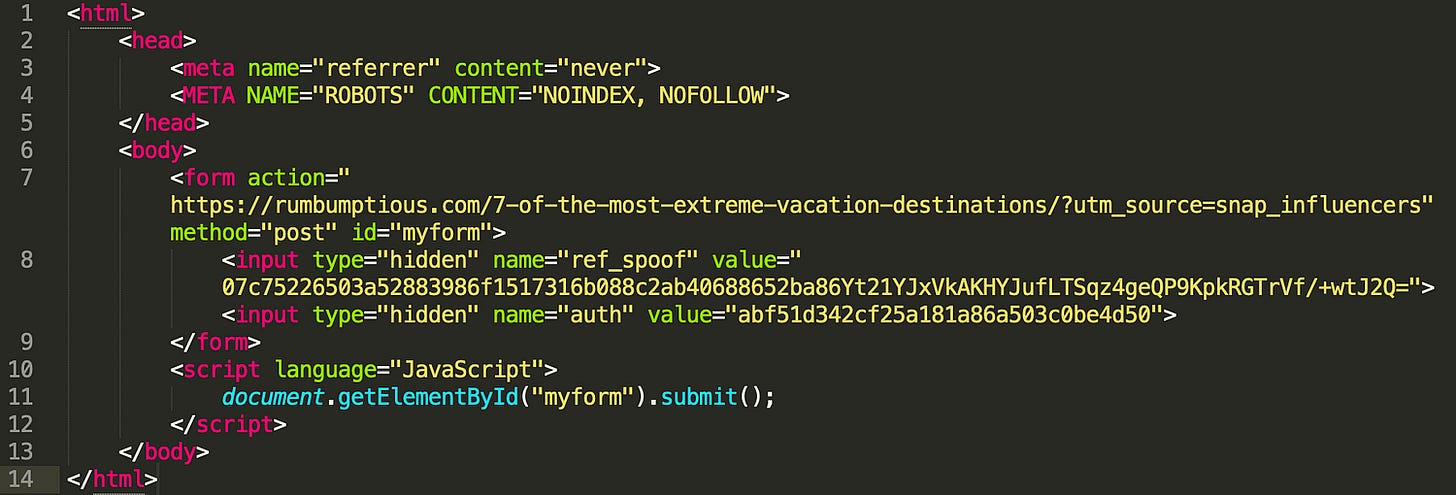
This is not exactly a creative tag. It’s an HTML document that dispatches an atypical redirection, but let’s pause to acknowledge that the meta tags serve a very important purpose.
This one is a directive that tells the browser how the referrer should be passed, or more specifically that it shouldn’t be passed at all:
<meta name=”referrer” content=”never”>Remember that the absence of a referrer is often an indicator of organic traffic!
This one tells crawlers (like googlebot) not to index the page or follow the links within:
<META NAME=”ROBOTS” CONTENT=”NOINDEX, NOFOLLOW”>For the coup de grâce, we have some code that dispatches a hidden POST request with two parameters called ref_spoof and auth to the following url:
hxxps://rumbumptious.com/7-of-the-most-extreme-vacation-destinations/?utm_source=snap_influencers
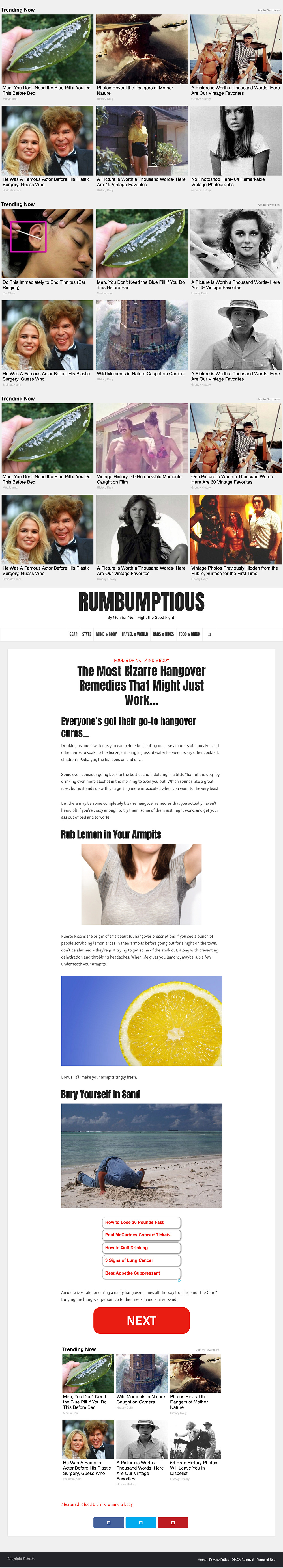
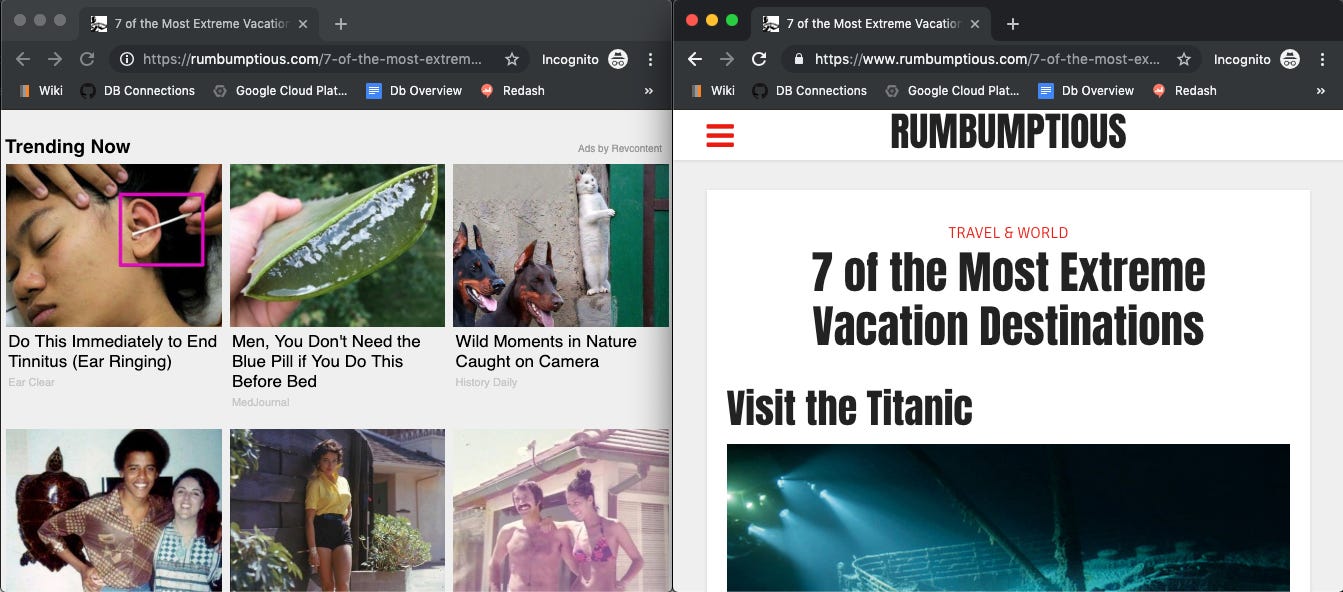
Here’s a screenshot of the page rendered as a POST request after the hidden form submitted:
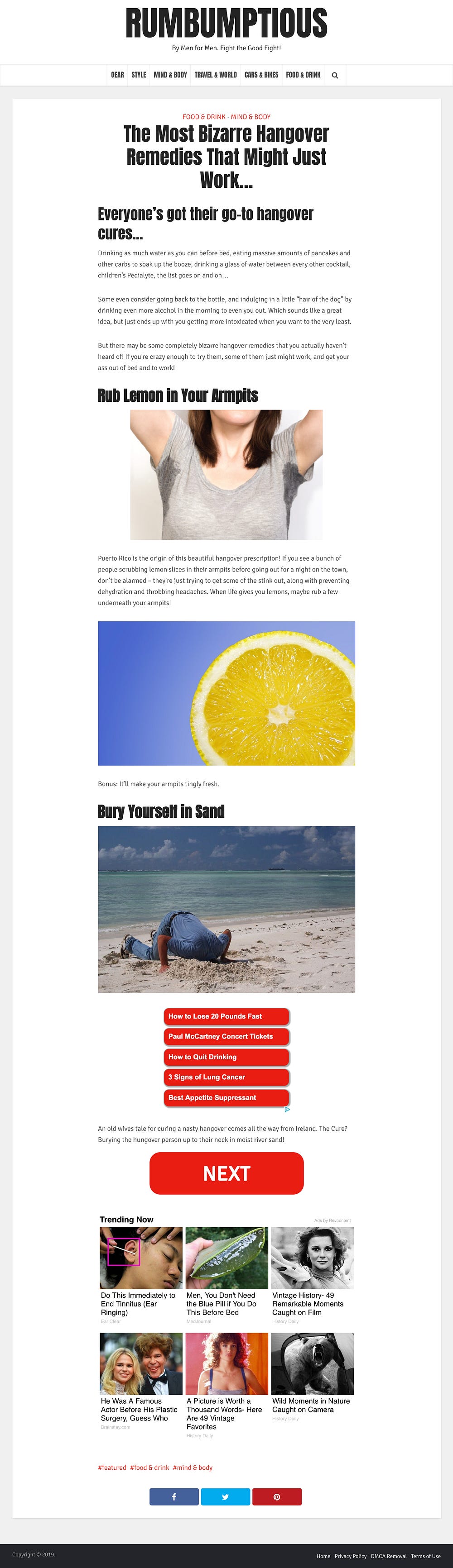
And here’s a screenshot of the page rendered when it’s loaded directly:
Let’s check them out side by side within the context of a viewport as well:
Having seen the images above, it should be pretty clear that the cloaked page masquerades as your run of the mill content site, but it is actually a cesspool of stuffed ads.
The techniques outlined above are actually not uncommon. Cloaking has been a favorite tool of SEO manipulators for the better part of a decade, if not longer, but The Dandelion Group stand out with their scale and persistence.
In the back half of 2018 alone, we have identified in the ballpark of 35 domains that follow the all_urls pattern above and act as either the creative launchpad or stuffed page (or both):
hxxp://anw.starpulse.com
hxxp://assets.brosive.com
hxxp://buzznow.co
hxxp://buzzwarp.com
hxxp://cafefame.com
hxxp://carsreviews.co
hxxp://carsstar.co
hxxp://epicguide.com
hxxp://funnyanimalnews.com
hxxp://gossipbuzz.com
hxxp://postsugar.com
hxxp://therugged.com
hxxp://thingsfinance.com
hxxp://truckhub.co
hxxp://urlish.com
hxxp://weedlio.com
hxxp://www.bitcoinusprice.com
hxxp://www.videoswebsites.com
hxxp://www.webbuildernews.com
hxxps://buzzwarp.com
hxxps://cafefame.com
hxxps://carsstar.co
hxxps://funnyanimalnews.com
hxxps://motorweb.co
hxxps://postsugar.com
hxxps://thingsfinance.com
hxxps://truckhub.co
hxxps://urlish.com
hxxps://viralshare.us
hxxps://www.culinarydiy.com
hxxps://www.enewsgossip.com
hxxps://www.gamingnewsweb.com
hxxps://www.moviesnewsweb.com
hxxps://www.viralmediatrends.com
hxxps://www.webbuildernews.com
hxxps://www.rumbumptious.com/Weedlio[.]com has been the most recurring culprit of the bunch with nearly 100 unique “ad tags”, but new sites, ad serving domains, and campaigns continue to surface on a regular basis.
These domains have appeared in over 3,500 unique scans in our system — most of which belong to campaigns that run at significant volumes through the display ad world.
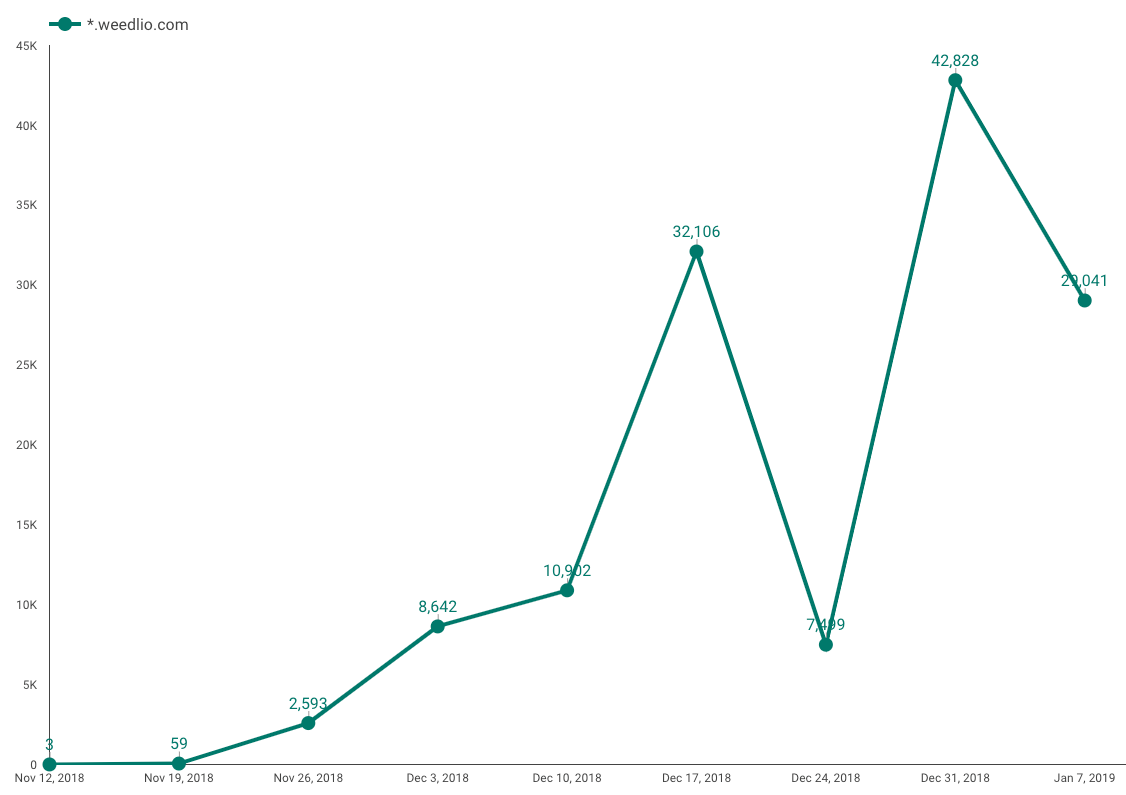
Here’s a visualization of our detection of weedlio[.]com during The Dandelion Group’s big Q4 push at the end of last year:
The Dandelion Group’s activity as described above is very much a case of cut and dried ad fraud, but the impact is further-reaching than the traditional fraud model will have you believe.
The obvious casualties here are the advertisers and platforms who are paying for their ads to be displayed outside of the boundaries of the viewable iframe, but legitimate publishers are victims here too.
The majority of programmatic ads have some kind of quality, viewability, or non-human traffic validation tags attached. The tags are deployed by platforms on the buy side or the advertisers themselves in order to track campaign performance, but inventory quality is measured as well.
While ads like this will not be marked as non-human-traffic, the ads stuffed into the iframe will certainly rank terribly on viewability. When fraudulent campaigns like the one described above run on a publisher at scale, the publisher’s reputation can get tainted by appearing as a source of non-viewable traffic. This makes the publisher’s inventory less desirable to buyers and will diminish CPMs and overall yield.
Archive: This article was originally published on our Confiant Medium blog on March 28, 2019