The Malvertising Campaign Lifecycle
This blog post is an investigation into the typical lifecycle of resources that serve malicious display ads, or as we like to call them, malvertisements.
Malvertisements are display ads that serve threatening Javascript, usually on a targeted basis, in order to hijack a browser, serve malware, or commit ad fraud. Basically, any display ad that delivers a code-based threat to the visitor’s browsing session can be thought of as a malvertisement.
Over the last few months, we have been averaging between 10 and 15 billion impressions monitored per month for our realtime blocking product. At a network wide block rate that hovers around 0.5% for security violations, this gives us a sample set of ~75MM incidents to look at from a birds eye view.
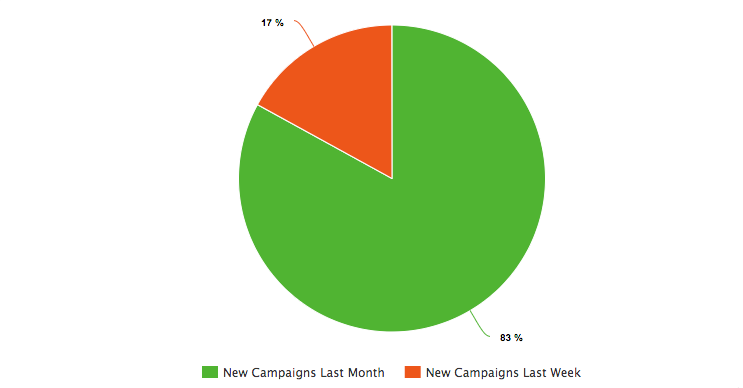
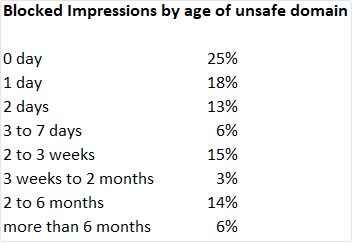
Here’s some trivia based on the last 30 days of data:
To put these statistics into words: malicious campaigns leave the display ad landscape just as quickly as they enter it.
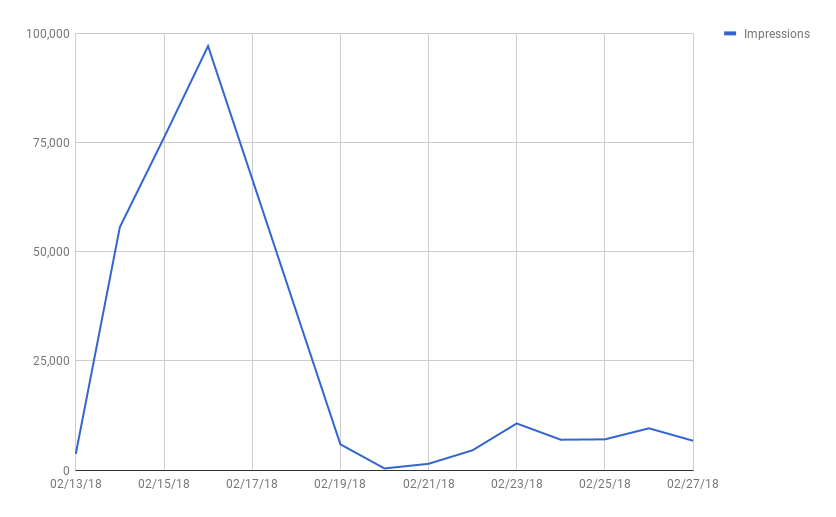
Here’s a helpful visualization:
The line graph above is the daily volume observed from a typical malvertising campaign as it happened upon our radar over the course of the month of February.
The campaign rapidly reaches peak volume within two days of its first appearance before it normalizes to a trickle. In the next 30 to 60 days it’s likely that we will never see this campaign again.
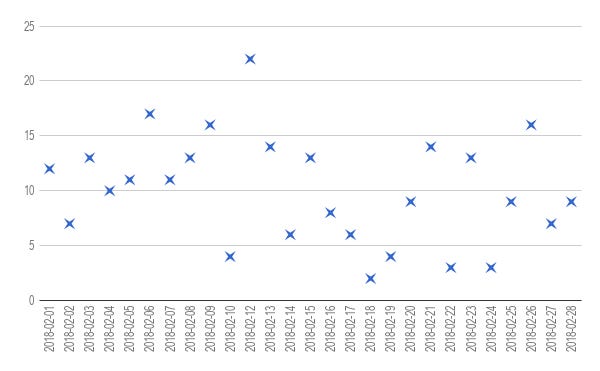
Here’s a visualization of the frequency with which campaigns like this appear:
This scatter plot shows how many new malvertising campaigns have been detected by day in the month of February. The majority of these campaigns will follow a similar pattern of rapidly peaking within 48 hours of launch before they fade away into relatively negligible volumes.
The rapid pace at which these campaigns appear, vanish, and rotate is what creates a true sense of urgency around immediate mitigation.
The Pitfalls of Ad Scanning
To-date, our industry has rallied around ad scanning in order to address many of the security and quality issues that plague display ads. Scanning entails the loading of ad tags into a managed software that emulates different browser environments, device types, locations, targeting criteria, etc. When the scanner triggers and detects an incident, it provides a report with the relevant details specific to that impression. Reporting usually includes items like a screenshot of the creative that rendered, the ad call chain, and a summary of the vendors involved.
Typically, when the scanning customer is sent a report related to an incident, resolution is a multifaceted process that looks like something like this:
The customer has to determine which of their upstream partners’ tag is attributed to the incident in the report and send the report upstream with a request to remove the offending creative or buyer from their inventory.
The customer’s upstream demand source has to analyze the third party report in order to determine which buyer to attribute the creative in question.
The demand partner then has to make the appropriate change within their ad serving platform and notify the scanning customer that the tag is now clear.
At this point, the scanning customer will either re-scan the tag for good measure, or proceed to set it live.
Ad scanning is certainly not without its merits —it does work to a large extent for issue discovery, but the typical remediation timeline is long and dragged out. Every brand new incident is a race against the clock due to the average malware campaign being most active during the first 48 hours. Unfortunately, the process described above often drags out much longer due to the back and forth required by two, three, or more parties.The other major challenge with ad scanning is the rising bar set by bad actors as they continue to experiment with detection and evasion.
Enter Confiant
The lengthy feedback loop described above was the main driver in our development of a realtime blocking product. While the aforementioned process does help to identify certain bad actors, it unfortunately does not actually solve the problem of a redirect. Realtime blocking does.
Archive: This article was originally published on our Confiant Medium blog on April 9, 2018