Tracking Software Weaponized by Criminals
Inside four months of joint research with Infoblox Threat Intel on the abuse of Keitaro Software.
Keitaro is an advertising performance tracker used by marketers and cyber criminals to route and measure traffic. It’s feature-rich, self-hosted, spins up in minutes on most hosting platforms, and can route visitors conditionally based on device type, geography, IP, and referrer. Criminals exploit it at scale.
Attackers have abused it for years. What nobody had done was study the abuse systematically across the full stack, at scale, over time. That’s what our joint research with Infoblox is.
How we built it
Confiant and Infoblox see the internet from different vantage points. Confiant has visibility across the digital advertising supply chain — billions of ad impressions a month, tracked through thousands of client-side integrations. We see the creative, the redirect, the cloaking behavior, and the moment a malicious ad reaches a real screen.
Infoblox operates at the DNS layer tracking how domains are registered, how infrastructure is built and burned, how threats move through spam, compromised websites, and web scans.
We examined four months of data starting October 1, 2025. What came back was a persistent, high-volume criminal ecosystem operating largely in plain sight.
What was running through it
15,500 malicious domains active during the study window. Roughly 9,000 registered specifically for this purpose. Traffic arriving through programmatic advertising, spam, social media, and compromised websites simultaneously, all routing through Keitaro instances, showing clean pages to anyone who looked like a reviewer.
Investment scams dominated. The pattern is consistent across actors: algorithmically registered domains, uniform web forms to capture victim contact details, fabricated news articles or endorsements to establish credibility.
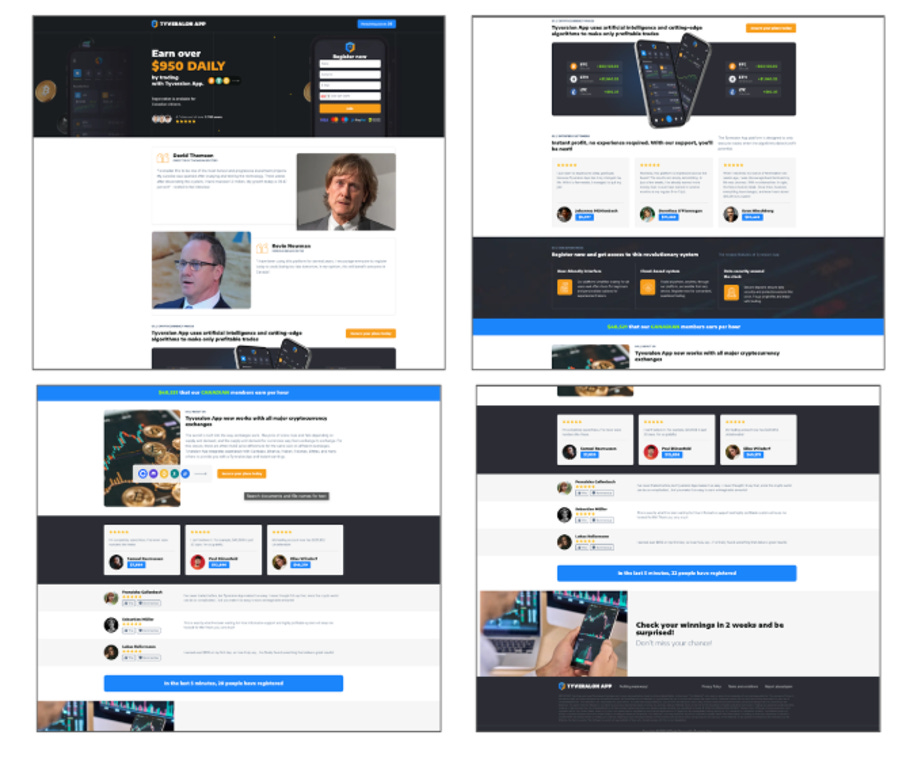
FaiKast runs deepfake video ads featuring AI-generated news anchors through the programmatic ecosystem. Victims click through to near-perfect replicas of legitimate news outlets including fake CBC broadcasts, fabricated quotes from real public figures, urgent calls to sign up for fraudulent cryptocurrency platforms. The operation targets France, the U.K., Canada, Japan, and Kazakhstan, with content localized to each market.
WickedWally targets U.S. seniors specifically with debt relief, grocery allowances, Medicare benefits, funeral expenses. The lures are AI-generated deepfake video ads designed to look like news reports, tied to current events. “Due to the USA tariffs release, you can erase your credit card debt for free until this Saturday.” Victims land on fake chatbots that qualify them for benefits that don’t exist, then route them to call centers that extract personal and financial information.
FishSteaks runs gamified giveaway scams impersonating American consumer brands — virtual prize boxes, falling confetti, multi-stage landing pages designed to maximize time-on-page and conversion. AI-generated placeholder assets swapped for brand logos as campaigns go live. Individual victim losses in tech support scam variants have reached beyond $40,000 in documented cases.
What happened when we reported it
Keitaro has been used by criminal actors for over a decade. The question we wanted to answer: was Apliteni, the company that makes Keitaro, turning a blind eye? Were they effectively a bulletproof tracker?
Since August 2025, we reported over 100 domains to Apliteni. They responded to each one. More than a dozen threat actor accounts were canceled. Through the exchanges, we verified that major malware actors including TA2726 were using illicit copies of the tracker.
This level of responsiveness matters, but it’s not the end of the problem. Actors rotate domains and creatives faster than any single remediation path can keep up with. However, it establishes a viable coordination channel, and it’s the model the industry needs more of.
Read Part 1: Inside Keitaro Abuse: A Persistent Stream of AI-Driven Investment Scams
The full research — methodology, indicators, actor profiles, infrastructure analysis — is out now. Parts 2 and 3 coming soon.
Co-authored with Infoblox Threat Intel.